Showing posts with label security. Show all posts
Showing posts with label security. Show all posts
Sunday 12 February 2012
Determine All Internet Connections And Corresponding Running Processes In Linux [How To]
Sometimes you might want to see all the internet connections being made by the running processes in the linux system. I am writing this small commandline trick to view all the internet connections using the lsof command.
lsof command is used to all the open files and the processes opening those files. All kind of resources such as disk, network connections, pipes, etc. are actually implemented as files in linux and the lsof command allows you to get the report regarding the opened files.
To view all the internet connections and the corresponding processes, we can simply use the -i switch as below:
The above command runs fine but is a little bit slow since it tries to resolve the network addresses to host names and port numbers to port names. So you might wish to use the command below for faster response from the lsof command.
Also, running the lsof command as the root(i.e. sudo lsof | grep -i listen or sudo lsof -i | grep -i listen) will give more extra outputs esp. the "LISTEN" ones i.e. the processes that are listening for incoming connections. This piece of information might be useful in determining the backdoors and rootkits but I've not yet explored into that.
I hope this little trick comes useful sometimes.
Read more...
lsof command is used to all the open files and the processes opening those files. All kind of resources such as disk, network connections, pipes, etc. are actually implemented as files in linux and the lsof command allows you to get the report regarding the opened files.
To view all the internet connections and the corresponding processes, we can simply use the -i switch as below:
samar@Techgaun:~$ lsof -i
The above command runs fine but is a little bit slow since it tries to resolve the network addresses to host names and port numbers to port names. So you might wish to use the command below for faster response from the lsof command.
samar@Techgaun:~$ lsof -i -Pn
Also, running the lsof command as the root(i.e. sudo lsof | grep -i listen or sudo lsof -i | grep -i listen) will give more extra outputs esp. the "LISTEN" ones i.e. the processes that are listening for incoming connections. This piece of information might be useful in determining the backdoors and rootkits but I've not yet explored into that.
I hope this little trick comes useful sometimes.
Read more...
Determine All Internet Connections And Corresponding Running Processes In Linux [How To]
2012-02-12T20:10:00+05:45
Cool Samar
internet|linux|lsof|security|tricks and tips|ubuntu|ubuntu 11.10|
Comments
Labels:
internet,
linux,
lsof,
security,
tricks and tips,
ubuntu,
ubuntu 11.10
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday 13 December 2011
Adding Static ARP Entry In ARP Table To Prevent ARP Spoofing Attacks
Since my hostel network is a switched network, there has been number of attempts of ARP spoofing attacks so I thought to share this small tip to prevent possible ARP spoofing attacks. Adding static ARP entry of the main server in your PC would possibly prevent RP spoofing attacks however I would warn you that some people have been saying that this is not still foolproof method. Theoretically I feel adding static ARP entries in the ARP table is the ultimate solution to prevent ARP spoofing and poisoning attacks.
Linux
Anyway, in linux its pretty straight-forward and the following command would add new static ARP entry:
Replace the IP_Addr and MAC_Addr fields with the necessary IP address and MAC address. For example, to add static ARP entry of my local gateway with IP 192.168.0.1 and MAC 00:14:d1:10:ea:1c, I would do:
To view all the entries in your system's ARP table, type the following command:
And you should see one of the entries similar to kubh-gateway.local (192.168.0.1) at 00:14:d1:10:ea:1c [ether] PERM on eth0.
Windows
Similar command as discussed above should work in Windows XP, however Windows 7 gave some problem while using the above command. I had a test on how to do that and I'm posting the series of screenshots on how to make static ARP entry in windows 7. Btw, I'm sorry that I'm not windows user and hence can't give much details.
arp -a output at beginning
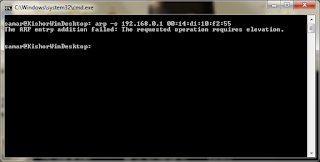
arp -s failure due to lack of privilege
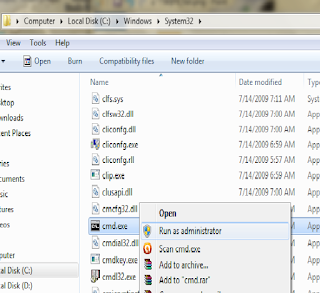
Running command prompt as admin
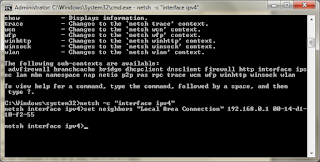
Adding static ARP entry
arp -a final output
Please go through the given screenshots to understand the steps done while adding static ARP entries in windows 7.
Read more...
Linux
Anyway, in linux its pretty straight-forward and the following command would add new static ARP entry:
sudo arp -s IP_Addr MAC_Addr
Replace the IP_Addr and MAC_Addr fields with the necessary IP address and MAC address. For example, to add static ARP entry of my local gateway with IP 192.168.0.1 and MAC 00:14:d1:10:ea:1c, I would do:
sudo arp -s 192.168.0.1 00:14:d1:10:ea:1c
To view all the entries in your system's ARP table, type the following command:
arp -a
And you should see one of the entries similar to kubh-gateway.local (192.168.0.1) at 00:14:d1:10:ea:1c [ether] PERM on eth0.
Windows
Similar command as discussed above should work in Windows XP, however Windows 7 gave some problem while using the above command. I had a test on how to do that and I'm posting the series of screenshots on how to make static ARP entry in windows 7. Btw, I'm sorry that I'm not windows user and hence can't give much details.
arp -a output at beginning
arp -s failure due to lack of privilege
Running command prompt as admin
Adding static ARP entry
arp -a final output
Please go through the given screenshots to understand the steps done while adding static ARP entries in windows 7.
Read more...
Adding Static ARP Entry In ARP Table To Prevent ARP Spoofing Attacks
2011-12-13T01:32:00+05:45
Cool Samar
arp spoofing|arp spoofing prevention|security|
Comments
Labels:
arp spoofing,
arp spoofing prevention,
security
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday 22 November 2011
How To Check Your Password Strength
With the increase in number of hackers and hack attacks, choosing strong and hard to guess passwords is one of the ways to keep yourself secure. While there are other numerous parameters to take care of to keep yourself secure, one of the primitives is choosing the strong password. In this post, I'll let you know how you can determine the strength of the password you choose to use.
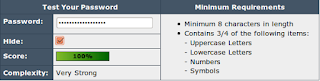
Strength of the password can be tested by studying the character combinations used in the password and there are some tools to assist you in this process.
The first tool is the password strength checker. This online tool gives a very comrehensive detail of the strenght of the password.
Another tool to test the strength of the password is to calculate the bruteforce attack time to retrieve the password from hash. One such tool is a excel template available HERE which gives the estimate of how fast a password is hacked by these widely available tools running on today's desktops. Another online tool for the similar purpose is howsecureismypassword.net which provides bruteforce time and informs if your password is the common one or not.
I hope you find this information useful. :)
Read more...
Strength of the password can be tested by studying the character combinations used in the password and there are some tools to assist you in this process.
The first tool is the password strength checker. This online tool gives a very comrehensive detail of the strenght of the password.
Another tool to test the strength of the password is to calculate the bruteforce attack time to retrieve the password from hash. One such tool is a excel template available HERE which gives the estimate of how fast a password is hacked by these widely available tools running on today's desktops. Another online tool for the similar purpose is howsecureismypassword.net which provides bruteforce time and informs if your password is the common one or not.
I hope you find this information useful. :)
Read more...
How To Check Your Password Strength
2011-11-22T10:54:00+05:45
Cool Samar
hacking|password hacking|security|
Comments
Labels:
hacking,
password hacking,
security
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Friday 18 November 2011
Securing LAMPP/XAMPP Installation
LAMPP by default leaves everything open and insecure allowing the possible intrusion to the system. In this post, I will show how you can secure yourself from the possible intrusions if you are using XAMPP and you are in the network. I am using LAMPP, the linux version of XAMPP to demonstrate the steps.
First lets run the security module of LAMPP to impose security in the LAMPP. To fix the security holes, type:
Now you will be asked with series of passwords if they are open to the intrusion. Check the following session of how I set the passwords for different daemons/services.
I hope this helps to fix the security issues quickly. However, there are other several issues that could be fixed to attain maximum level of security.
EDIT: Check this link for more detailed information than mine.
Read more...
First lets run the security module of LAMPP to impose security in the LAMPP. To fix the security holes, type:
sudo /opt/lampp/lampp security
Now you will be asked with series of passwords if they are open to the intrusion. Check the following session of how I set the passwords for different daemons/services.
samar@Techgaun:~$ sudo /opt/lampp/lampp security
XAMPP: Quick security check...
XAMPP: Your XAMPP pages are NOT secured by a password.
XAMPP: Do you want to set a password? [yes] yes
XAMPP: Password:
XAMPP: Password (again):
XAMPP: Password protection active. Please use 'lampp' as user name!
XAMPP: The MySQL/phpMyAdmin user pma has no password set!!!
XAMPP: Do you want to set a password? [yes] yes
XAMPP: Password:
XAMPP: Password (again):
XAMPP: Setting new MySQL pma password.
XAMPP: Setting phpMyAdmin's pma password to the new one.
XAMPP: MySQL has no root passwort set!!!
XAMPP: Do you want to set a password? [yes] yes
XAMPP: Write the password somewhere down to make sure you won't forget it!!!
XAMPP: Password:
XAMPP: Password (again):
XAMPP: Setting new MySQL root password.
XAMPP: Change phpMyAdmin's authentication method.
XAMPP: The FTP password for user 'nobody' is still set to 'lampp'.
XAMPP: Do you want to change the password? [yes] yes
XAMPP: Password:
XAMPP: Password (again):
XAMPP: Reload ProFTPD...
XAMPP: Done.
XAMPP: Quick security check...
XAMPP: Your XAMPP pages are NOT secured by a password.
XAMPP: Do you want to set a password? [yes] yes
XAMPP: Password:
XAMPP: Password (again):
XAMPP: Password protection active. Please use 'lampp' as user name!
XAMPP: The MySQL/phpMyAdmin user pma has no password set!!!
XAMPP: Do you want to set a password? [yes] yes
XAMPP: Password:
XAMPP: Password (again):
XAMPP: Setting new MySQL pma password.
XAMPP: Setting phpMyAdmin's pma password to the new one.
XAMPP: MySQL has no root passwort set!!!
XAMPP: Do you want to set a password? [yes] yes
XAMPP: Write the password somewhere down to make sure you won't forget it!!!
XAMPP: Password:
XAMPP: Password (again):
XAMPP: Setting new MySQL root password.
XAMPP: Change phpMyAdmin's authentication method.
XAMPP: The FTP password for user 'nobody' is still set to 'lampp'.
XAMPP: Do you want to change the password? [yes] yes
XAMPP: Password:
XAMPP: Password (again):
XAMPP: Reload ProFTPD...
XAMPP: Done.
I hope this helps to fix the security issues quickly. However, there are other several issues that could be fixed to attain maximum level of security.
EDIT: Check this link for more detailed information than mine.
Read more...
Securing LAMPP/XAMPP Installation
2011-11-18T21:53:00+05:45
Cool Samar
lampp hardening|security|
Comments
Labels:
lampp hardening,
security
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Wednesday 26 October 2011
Lists of Various Steganographic Tools
Steganography is the art and science of hiding information such that only the sender and recipient can read that hidden piece of information. While the cryptography is focussed on making message unreadable, steganography focusses on data hiding and hence combination of both can give better security in most cases.
As mentioned earlier, steganography is the art of hiding information and can be done in many ways. For instance, simplest forms of steganography would be toinsert each character of hidden message in the Nth position of each word in a sentence so that recipient takes Nth letters of each words to reconstruct the message. While this was very basic example, steganography has no bounds and one can hide messages within images, audios, videos, source codes, etc and this involves some sort of creation to increase the obscurity of the hidden message. Wikipedia entry gives far much deeper information on steganography tool and I would like to recommend you to read it.
To make digital steganography easier, numerous tools have been developed and I'm listing some of them here.
1) Hide in Picture: Hide In Picture is a program that allows you to conceal files inside bitmap pictures, using a password. The pictures look like normal images, so people will not suspect there is hidden data in them.
2) wbStego: wbStego4 offers steganography in bitmaps, text files, HTML files and PDF files. It is has two very user-friendly interfaces and is ideal for securely transmitting data online or adding copyright information, especially with the copyright information manager.
3) Hide4PGP: Hide4PGP is a freeware program distributed as source code in ANSI C and precompiled executables for DOS (any version but 1.x), OS/2 (Warp and up), and the Win32 console (9x and NT). It's purpose is to hide any data in a way that the viewer or listener does not recognize any difference. It supports BMP, WAV and VOC file formats.
4) MP3Stego: Hide files within mp3 files. MP3Stego will hide information in MP3 files during the compression process. The data is first compressed, encrypted and then hidden in the MP3 bit stream.
5) TextHide: Simple text steganography
6) GifShuffle: gifshuffle is used to conceal messages in GIF images by shuffling the colourmap, which leaves the image visibly unchanged. gifshuffle works with all GIF images, including those with transparency and animation, and in addition provides compression and encryption of the concealed message.
7) Snow: snow is used to conceal messages in ASCII text by appending whitespace to the end of lines. Because spaces and tabs are generally not visible in text viewers, the message is effectively hidden from casual observers. And if the built-in encryption is used, the message cannot be read even if it is detected.
8) Camouflage: Camouflage allows you to hide files by scrambling them and then attaching them to the file of your choice. This camouflaged file then looks and behaves like a normal file, and can be stored, used or emailed without attracting attention.
9) OpenPuff: OpenPuff is a professional steganography tool, with unique features you won't find among any other free or commercial software. OpenPuff is 100% free and suitable for highly sensitive data covert transmission. Its very advanced tool with support to images, audios, videos, flash, adobe.
10) SteganRTP: Steganography tool which establishes a full-duplex steganographic data transfer protocol utilizing Real-time Transfer Protocol (RTP) packet payloads as the cover medium. The tool provides interactive chat, file transfer, and remote shell access. A network steganographic tool.
Read more...
As mentioned earlier, steganography is the art of hiding information and can be done in many ways. For instance, simplest forms of steganography would be toinsert each character of hidden message in the Nth position of each word in a sentence so that recipient takes Nth letters of each words to reconstruct the message. While this was very basic example, steganography has no bounds and one can hide messages within images, audios, videos, source codes, etc and this involves some sort of creation to increase the obscurity of the hidden message. Wikipedia entry gives far much deeper information on steganography tool and I would like to recommend you to read it.
To make digital steganography easier, numerous tools have been developed and I'm listing some of them here.
1) Hide in Picture: Hide In Picture is a program that allows you to conceal files inside bitmap pictures, using a password. The pictures look like normal images, so people will not suspect there is hidden data in them.
2) wbStego: wbStego4 offers steganography in bitmaps, text files, HTML files and PDF files. It is has two very user-friendly interfaces and is ideal for securely transmitting data online or adding copyright information, especially with the copyright information manager.
3) Hide4PGP: Hide4PGP is a freeware program distributed as source code in ANSI C and precompiled executables for DOS (any version but 1.x), OS/2 (Warp and up), and the Win32 console (9x and NT). It's purpose is to hide any data in a way that the viewer or listener does not recognize any difference. It supports BMP, WAV and VOC file formats.
4) MP3Stego: Hide files within mp3 files. MP3Stego will hide information in MP3 files during the compression process. The data is first compressed, encrypted and then hidden in the MP3 bit stream.
5) TextHide: Simple text steganography
6) GifShuffle: gifshuffle is used to conceal messages in GIF images by shuffling the colourmap, which leaves the image visibly unchanged. gifshuffle works with all GIF images, including those with transparency and animation, and in addition provides compression and encryption of the concealed message.
7) Snow: snow is used to conceal messages in ASCII text by appending whitespace to the end of lines. Because spaces and tabs are generally not visible in text viewers, the message is effectively hidden from casual observers. And if the built-in encryption is used, the message cannot be read even if it is detected.
8) Camouflage: Camouflage allows you to hide files by scrambling them and then attaching them to the file of your choice. This camouflaged file then looks and behaves like a normal file, and can be stored, used or emailed without attracting attention.
9) OpenPuff: OpenPuff is a professional steganography tool, with unique features you won't find among any other free or commercial software. OpenPuff is 100% free and suitable for highly sensitive data covert transmission. Its very advanced tool with support to images, audios, videos, flash, adobe.
10) SteganRTP: Steganography tool which establishes a full-duplex steganographic data transfer protocol utilizing Real-time Transfer Protocol (RTP) packet payloads as the cover medium. The tool provides interactive chat, file transfer, and remote shell access. A network steganographic tool.
Read more...
Lists of Various Steganographic Tools
2011-10-26T17:38:00+05:45
Cool Samar
security|software|steganography|
Comments
Labels:
security,
software,
steganography
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Monday 26 September 2011
RSS and Related Security Issues For Business People
While RSS is a very simple way to expand your business and nothing complex is involved in RSS feed systems, you should never underestimate the security issues in any digitized systems, not even in really simple technology like RSS. A business company should always be aware of possible security risks in any system they are employing to help them in their tasks.
Most of you might believe there would not be much security issues in RSS feeds and feel that you need not worry about any cases of exploiting of your system but that's just a myth. Malicious attackers can inject scripts inside the feeds and affect thousands of feed readers with even a single vulnerability discovered in the popular RSS reader or aggregators.
Bad HTML or javascript can be injected as malware inside the feeds and if your business is gathering content from other sources and adding them to feeds, your feeds are likely to be affected by such malwares. Such scripts are generally injected in the feed titles, descriptions, links and other components of the RSS feeds. The scripts injected can exploit the possible vulnerabilities in the RSS readers of your subscribers leading to possible control of your subscriber's PC by the attacker. This can open possible backdoors by the installation of trojans or keyloggers using the proper exploits such as browser exploits, activex exploits, etc. and let the attacker steal the data by using possible local zone security attacks which can be the worst thing you can imagine happening to your business as customers are the life blood of every business and you engage customers everywhere. And if your customers are affected, then ultimately your business will be affected. Hence extreme care should be taken while importing content from other sources to develop your RSS contents.
Many times business owners like to include the comments from subscribers in the RSS contents and mostly they hardly watch the actual content in those comments. There is always a possibility of injection of malicious scripts in those comments as well. So proper filtering and stripping mechanism has to be employed before storing new contents to your RSS feeds rather than just storing those comments in the feed contents. The HTML tags such as script, embed, object, etc. are the ones that must be stripped out in most cases to avoid possible security issues. Also, using safe and secure RSS reader or aggregator is a good approach to RSS security. So you should choose the most secure RSS reader or aggregator from the available ones and suggest those to your subscribers. Also, make sure that your customers and employees use the latest and patched version of the reader so that maximum level of security is ensured.
In many cases, the RSS generators and other services in the RSS servers are also prone to security attacks and the attackers might be able to gain certain level of privilege in the system. In such case, the attackers can replace the original RSS feeds with their own affected version of RSS feeds which will then be delivered to your customers affecting your customers and your business as well. This can be devastating as this might lead not only to the script injections in the feeds but also stealing of many sensitive information from the server. For example, if your RSS server is used to host your business website or maybe for file sharing, the critical data related to them might be compromised as well. So proper security assessment of the server and network from the security professionals is necessary before taking your system live for production usage.
As a business owner, you must understand that security is a necessity in any system, be it a physical system or be it a digitized and online system and RSS is not an exception to this. If you want to succeed as a business owner, you should never underestimate the need of security and privacy and you should employ proper level of security as discussed above in the RSS system. Security in RSS system will ensure gaining of customers and expansion and promotion of your business so do not miss security practices in your RSS feed contents.
Read more...
Most of you might believe there would not be much security issues in RSS feeds and feel that you need not worry about any cases of exploiting of your system but that's just a myth. Malicious attackers can inject scripts inside the feeds and affect thousands of feed readers with even a single vulnerability discovered in the popular RSS reader or aggregators.
Bad HTML or javascript can be injected as malware inside the feeds and if your business is gathering content from other sources and adding them to feeds, your feeds are likely to be affected by such malwares. Such scripts are generally injected in the feed titles, descriptions, links and other components of the RSS feeds. The scripts injected can exploit the possible vulnerabilities in the RSS readers of your subscribers leading to possible control of your subscriber's PC by the attacker. This can open possible backdoors by the installation of trojans or keyloggers using the proper exploits such as browser exploits, activex exploits, etc. and let the attacker steal the data by using possible local zone security attacks which can be the worst thing you can imagine happening to your business as customers are the life blood of every business and you engage customers everywhere. And if your customers are affected, then ultimately your business will be affected. Hence extreme care should be taken while importing content from other sources to develop your RSS contents.
Many times business owners like to include the comments from subscribers in the RSS contents and mostly they hardly watch the actual content in those comments. There is always a possibility of injection of malicious scripts in those comments as well. So proper filtering and stripping mechanism has to be employed before storing new contents to your RSS feeds rather than just storing those comments in the feed contents. The HTML tags such as script, embed, object, etc. are the ones that must be stripped out in most cases to avoid possible security issues. Also, using safe and secure RSS reader or aggregator is a good approach to RSS security. So you should choose the most secure RSS reader or aggregator from the available ones and suggest those to your subscribers. Also, make sure that your customers and employees use the latest and patched version of the reader so that maximum level of security is ensured.
In many cases, the RSS generators and other services in the RSS servers are also prone to security attacks and the attackers might be able to gain certain level of privilege in the system. In such case, the attackers can replace the original RSS feeds with their own affected version of RSS feeds which will then be delivered to your customers affecting your customers and your business as well. This can be devastating as this might lead not only to the script injections in the feeds but also stealing of many sensitive information from the server. For example, if your RSS server is used to host your business website or maybe for file sharing, the critical data related to them might be compromised as well. So proper security assessment of the server and network from the security professionals is necessary before taking your system live for production usage.
As a business owner, you must understand that security is a necessity in any system, be it a physical system or be it a digitized and online system and RSS is not an exception to this. If you want to succeed as a business owner, you should never underestimate the need of security and privacy and you should employ proper level of security as discussed above in the RSS system. Security in RSS system will ensure gaining of customers and expansion and promotion of your business so do not miss security practices in your RSS feed contents.
Read more...
RSS and Related Security Issues For Business People
2011-09-26T16:24:00+05:45
Cool Samar
beginner|rss|security|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Monday 12 September 2011
Nixory - A Light Antispyware Tool
Nixory is a light and handy open source antispyware tool aimed at removing malicious tracking cookies. It currently supports Mozilla Firefox, Google Chrome and Internet Explorer and it runs on all major OS including Windows, Linux and MacOSx.
For more information and download, visit nixory sourceforge page.
Read more...
For more information and download, visit nixory sourceforge page.
Read more...
Nixory - A Light Antispyware Tool
2011-09-12T09:32:00+05:45
Cool Samar
browser|security|software|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Friday 19 August 2011
Open Source Anti-theft Solution For MAC, PCs and Phones
Prey is an open source application that helps us track the lost laptops or phones. Prey lets you keep track of your phone or laptop at all times, and will help you find it if it ever gets lost or stolen. It's lightweight, open source software, and free for anyone to use.
In order to understand more about the project, visit the Official website.
Also try this video tutorial for configuring the Prey application.
I hope it becomes useful for you. :)
Read more...
In order to understand more about the project, visit the Official website.
Also try this video tutorial for configuring the Prey application.
I hope it becomes useful for you. :)
Read more...
Open Source Anti-theft Solution For MAC, PCs and Phones
2011-08-19T13:33:00+05:45
Cool Samar
anti-theft|security|software|
Comments
Labels:
anti-theft,
security,
software
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Anonymous and Encrypted Torrent Download With Anomos
Anomos is a free and open source standalone anonymous and encrypted torrent client so if you are too concerned about anonymity, why not try this torrent client. Anomos is available for all major platforms including windows, linux and OSX.
Anomos Quote:
Anomos is a pseudonymous, encrypted multi-peer-to-peer file distribution protocol. It is based on the peer/tracker concept of BitTorrent in combination with an onion routing anonymization layer, with the added benefit of end-to-end encryption. By combining these technologies, we have created a platform where by no party outside of the trusted tracker will have any information about who a peer is or what they are downloading.
smwhite
Anomos is designed to be easy to use – you won’t even be aware of the security that it provides. Anybody who is already familiar with BitTorrent won’t have to do anything differently, other than use ‘atorrent’ files rather than ‘torrent’ files.
For more technical details, please see this blog post.
For downloads and more information, visit the Anomos Official Site.
Read more...
Anomos Quote:
Anomos is a pseudonymous, encrypted multi-peer-to-peer file distribution protocol. It is based on the peer/tracker concept of BitTorrent in combination with an onion routing anonymization layer, with the added benefit of end-to-end encryption. By combining these technologies, we have created a platform where by no party outside of the trusted tracker will have any information about who a peer is or what they are downloading.
smwhite
Anomos is designed to be easy to use – you won’t even be aware of the security that it provides. Anybody who is already familiar with BitTorrent won’t have to do anything differently, other than use ‘atorrent’ files rather than ‘torrent’ files.
For more technical details, please see this blog post.
For downloads and more information, visit the Anomos Official Site.
Read more...
Anonymous and Encrypted Torrent Download With Anomos
2011-08-19T12:45:00+05:45
Cool Samar
anonymity|security|torrent|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
BleachBit : Disk Cleanup Utility For Windows and Linux
Bleachbit is a free and open-source utility that can be used to clean Junk space to free disk space and maintain privacy.
BleachBit quickly frees disk space and tirelessly guards your privacy. Free cache, delete cookies, clear Internet history, shred temporary files, delete logs, and discard junk you didn't know was there. Designed for Linux and Windows systems, it wipes clean 90 applications including Firefox, Internet Explorer, Adobe Flash, Google Chrome, Opera, Safari,and more. Beyond simply deleting files, BleachBit includes advanced features such as shredding files to prevent recovery, wiping free disk space to hide traces of files deleted by other applications, and vacuuming Firefox to make it faster. Better than free, BleachBit is open source.
Downloads and more information available at Bleachbit SourceForge Page.
Read more...
BleachBit quickly frees disk space and tirelessly guards your privacy. Free cache, delete cookies, clear Internet history, shred temporary files, delete logs, and discard junk you didn't know was there. Designed for Linux and Windows systems, it wipes clean 90 applications including Firefox, Internet Explorer, Adobe Flash, Google Chrome, Opera, Safari,and more. Beyond simply deleting files, BleachBit includes advanced features such as shredding files to prevent recovery, wiping free disk space to hide traces of files deleted by other applications, and vacuuming Firefox to make it faster. Better than free, BleachBit is open source.
Downloads and more information available at Bleachbit SourceForge Page.
Read more...
BleachBit : Disk Cleanup Utility For Windows and Linux
2011-08-19T12:24:00+05:45
Cool Samar
linux|security|software|windows|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
IPV6 Attacking Toolkit - THC-ipV6 Toolkit Released
The famous hackers group The Hacker Choice(THC) has released a set of tools to attack the IPv6 protocol. IPv6 is the descendant of IPv4 protocol which was purposed due to exhaustion of the IPv4 pool.
THC writes:
THC is proud to be the first who are releasing an comprehensive attack toolkit for the IPv6 protocol suite. It comprises of state-of-the-art tools for alive scanning, man-in-the-middle attacks, denial-of-service etc. which exploits inherent vulnerabilities in IPv6. Included is a fast and easy to use packet crafting library to create your own attack tools.
For more information on the project, visit the THC IPv6 Project Page.
Download Here
Read more...
THC writes:
THC is proud to be the first who are releasing an comprehensive attack toolkit for the IPv6 protocol suite. It comprises of state-of-the-art tools for alive scanning, man-in-the-middle attacks, denial-of-service etc. which exploits inherent vulnerabilities in IPv6. Included is a fast and easy to use packet crafting library to create your own attack tools.
For more information on the project, visit the THC IPv6 Project Page.
Download Here
Read more...
IPV6 Attacking Toolkit - THC-ipV6 Toolkit Released
2011-08-19T09:59:00+05:45
Cool Samar
hacking|internet protocol|security|software|
Comments
Labels:
hacking,
internet protocol,
security,
software
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Backtrack 5 R1 Released
The most widely used linux-based penetration testing distro, BackTrack had a new release yesterday. Backtrack 5 R1 was released on August 18 which adds 30 new tools in the famous hacker's distro.
Offsec team says:
We are really happy with this release, and believe that as with every release, this is our best one yet. Some pesky issues such as rfkill in VMWare with rtl8187 issues have been fixed, which provides for a much more solid experience with BackTrack.
We’ve released Gnome and KDE ISO images for 32 and 64 bit (no arm this release, sorry!), as well as a VMWare image of a 32 bit Gnome install, with VMWare Tools pre-installed.
For downloads, visit Backtrack Download Page.
Read more...
Offsec team says:
We are really happy with this release, and believe that as with every release, this is our best one yet. Some pesky issues such as rfkill in VMWare with rtl8187 issues have been fixed, which provides for a much more solid experience with BackTrack.
We’ve released Gnome and KDE ISO images for 32 and 64 bit (no arm this release, sorry!), as well as a VMWare image of a 32 bit Gnome install, with VMWare Tools pre-installed.
For downloads, visit Backtrack Download Page.
Read more...
Backtrack 5 R1 Released
2011-08-19T09:25:00+05:45
Cool Samar
backtrack|hacking|linux|security|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Monday 25 July 2011
Wireshark 1.6.1 stable version released
The stable version of wireshark 1.6.1 has been released lately (July 18). Wireshark is the world's foremost network protocol analyzer. It lets you capture and interactively browse the traffic running on a computer network. It is the de facto standard across many industries and educational institutions.
To download wireshark, visit this link.
Read more...
To download wireshark, visit this link.
Read more...
Wireshark 1.6.1 stable version released
2011-07-25T21:00:00+05:45
Cool Samar
hacking|security|sniffer|wireshark|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday 12 July 2011
Search Exploits & Vulnerability With Exploitsearch.net
The site, www.exploitsearch.net, is an attempt at cross referencing data from various sources and making the resulting database available to everyone.
Unlike other exploit search engines which are simply custom google searches, this site actually crawls the source sites and parses the contained data. Once the data is collected and parsed, it is inserted into the www.exploitsearch.net database and becomes available for searching.
www.exploitsearch.net
Currently utilizes data from NVD, OSVDB, SecurityFocus, Exploit-DB, Metasploit, Nessus, OpenVAS, and PacketStorm.Comes handy for better results. :)
Read more...
Unlike other exploit search engines which are simply custom google searches, this site actually crawls the source sites and parses the contained data. Once the data is collected and parsed, it is inserted into the www.exploitsearch.net database and becomes available for searching.
www.exploitsearch.net
Currently utilizes data from NVD, OSVDB, SecurityFocus, Exploit-DB, Metasploit, Nessus, OpenVAS, and PacketStorm.Comes handy for better results. :)
Read more...
Search Exploits & Vulnerability With Exploitsearch.net
2011-07-12T23:13:00+05:45
Cool Samar
hacking|security|useful website|
Comments
Labels:
hacking,
security,
useful website
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday 30 June 2011
Mobius Forensic Toolkit 0.5.8 Is Out
Mobius Forensic Toolkit is a forensic framework written in Python/GTK that manages cases and case items, providing an abstract interface for developing extensions. Cases and item categories are defined using XML files for easy integration with other tools.
Changes: The Hive (registry viewer) features three new reports: email accounts, TCP/IP interfaces, and computer descriptions. All registry reports can be exported as CSV and the user password report can be exported in a format suitable for John the Ripper as well. Minor improvements were made.
For more information and downloads, visit the official link here.
Read more...
Changes: The Hive (registry viewer) features three new reports: email accounts, TCP/IP interfaces, and computer descriptions. All registry reports can be exported as CSV and the user password report can be exported in a format suitable for John the Ripper as well. Minor improvements were made.
For more information and downloads, visit the official link here.
Read more...
Mobius Forensic Toolkit 0.5.8 Is Out
2011-06-30T21:00:00+05:45
Cool Samar
forensic|security|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Wednesday 29 June 2011
Source Code Auditing With Graudit
Graudit is a simple script and signature sets that allows you to find potential security flaws in source code using the GNU utility grep. It's comparable to other static analysis applications like RATS, SWAAT and flaw-finder while keeping the technical requirements to a minimum and being very flexible.
The tool can be downloaded from HERE
Read more...
The tool can be downloaded from HERE
Read more...
Source Code Auditing With Graudit
2011-06-29T19:13:00+05:45
Cool Samar
security|software|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday 9 June 2011
Advanced HTTP Fingerprinting With httprecon
One of the first steps in web server hacking involves fingerprinting to gather information regarding the web server and various mods applied to it. Fingerprinting the web server manually can be cumbersome so some good folks have developed an advanced open-source fingerprinting tool known as httprecon
*Description from official webpage:
The httprecon project is doing some research in the field of web server fingerprinting, also known as http fingerprinting. The goal is the highly accurate identification of given httpd implementations. This is very important within professional vulnerability analysis.
Besides the discussion of different approaches and the documentation of gathered results also an implementation for automated analysis is provided. This software shall improve the easyness and efficiency of this kind of enumeration. Traditional approaches as like banner-grabbing, status code enumeration and header ordering analysis are used. However, many other analysis techniques were introduced to increase the possibilities of accurate web server fingerprinting.
Check the Page of httprecon project
Read more...
*Description from official webpage:
The httprecon project is doing some research in the field of web server fingerprinting, also known as http fingerprinting. The goal is the highly accurate identification of given httpd implementations. This is very important within professional vulnerability analysis.
Besides the discussion of different approaches and the documentation of gathered results also an implementation for automated analysis is provided. This software shall improve the easyness and efficiency of this kind of enumeration. Traditional approaches as like banner-grabbing, status code enumeration and header ordering analysis are used. However, many other analysis techniques were introduced to increase the possibilities of accurate web server fingerprinting.
Check the Page of httprecon project
Read more...
Advanced HTTP Fingerprinting With httprecon
2011-06-09T23:26:00+05:45
Cool Samar
hacking|security|software|useful website|
Comments
Labels:
hacking,
security,
software,
useful website
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday 10 May 2011
Learn Web Hacking With WackoPicko
WackoPicko is a website that contains known vulnerabilities. It can prove as a very efficient way to master web hacking skills. This project is similar to Damn Vulnerable Web Application and is a collection of common web vulnerabilities.
For more information and downloads, you can check the WackoPicko github page.
Vulnerabilities
Reflected XSS
http://localhost/pictures/search.php?query=blah
The query parameter is vulnerable.
Stored XSS
http://localhost/guestbook.php
The comment field is vulnerable.
SessionID vulnerability
http://localhost/admin/login.php
The session cookie value is admin_session, which is an auto-incrementing value.
Stored SQL Injection
http://localhost/users/register.php -> http://localhost/users/similar.php
The first name field of the register users form contains a stored SQL injection which is then used unsanitized on the similar users page.
Reflected SQL Injection
http://localhost/users/login.php
The username field is vulnerable.
Directory Traversal
http://localhost/pictures/upload.php
The tag field has a directory traversal vulnerability enabling a malicious users to overwrite any file the web server uses has access to.
Multi-Step Stored XSS
http://localhost/pictures/view.php?picid=3
The comment field is vulnerable to XSS, however must go through a preview form.
Forceful Browsing
http://localhost/pictures/highquality.php?picid=3&key=highquality
The user doesn't have to purchase the picture to see the high quality version.
Command-line Injection
http://localhost/passcheck.php
The password field is vulnerable to a command line injections.
File Inclusion
http://localhost/admin/index.php?page=login
The page is vulnerable to a file inclusion vulnerability, however you have to include at the end.
Parameter Manipulation
http://localhost/users/sample.php?userid=1
The userid parameter can be manipulated to see any user's page when you need to be logged in otherwise.
Reflected XSS Behind JavaScript
http://localhost/piccheck.php
The name parameter is vulnerable.
Logic Flaw
http://localhost/cart/review.php
A coupon can be applied multiple times reducing the price of an order to zero. The coupon in the initial data is SUPERYOU21.
Reflected XSS Behind a Flash Form
http://localhost/submitname.php
The value parameter is vulnerable.
Weak username/password
https://localhost/admin/login.php
There is a default username/password combination of admin/admin.
Read more...
For more information and downloads, you can check the WackoPicko github page.
Vulnerabilities
Reflected XSS
http://localhost/pictures/search.php?query=blah
The query parameter is vulnerable.
Stored XSS
http://localhost/guestbook.php
The comment field is vulnerable.
SessionID vulnerability
http://localhost/admin/login.php
The session cookie value is admin_session, which is an auto-incrementing value.
Stored SQL Injection
http://localhost/users/register.php -> http://localhost/users/similar.php
The first name field of the register users form contains a stored SQL injection which is then used unsanitized on the similar users page.
Reflected SQL Injection
http://localhost/users/login.php
The username field is vulnerable.
Directory Traversal
http://localhost/pictures/upload.php
The tag field has a directory traversal vulnerability enabling a malicious users to overwrite any file the web server uses has access to.
Multi-Step Stored XSS
http://localhost/pictures/view.php?picid=3
The comment field is vulnerable to XSS, however must go through a preview form.
Forceful Browsing
http://localhost/pictures/highquality.php?picid=3&key=highquality
The user doesn't have to purchase the picture to see the high quality version.
Command-line Injection
http://localhost/passcheck.php
The password field is vulnerable to a command line injections.
File Inclusion
http://localhost/admin/index.php?page=login
The page is vulnerable to a file inclusion vulnerability, however you have to include at the end.
Parameter Manipulation
http://localhost/users/sample.php?userid=1
The userid parameter can be manipulated to see any user's page when you need to be logged in otherwise.
Reflected XSS Behind JavaScript
http://localhost/piccheck.php
The name parameter is vulnerable.
Logic Flaw
http://localhost/cart/review.php
A coupon can be applied multiple times reducing the price of an order to zero. The coupon in the initial data is SUPERYOU21.
Reflected XSS Behind a Flash Form
http://localhost/submitname.php
The value parameter is vulnerable.
Weak username/password
https://localhost/admin/login.php
There is a default username/password combination of admin/admin.
Read more...
Learn Web Hacking With WackoPicko
2011-05-10T22:46:00+05:45
Cool Samar
cross site scripting|hacking|remote code exection|security|security bypass|sql injection|useful website|
Comments
Labels:
cross site scripting,
hacking,
remote code exection,
security,
security bypass,
sql injection,
useful website
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Sunday 24 April 2011
Automatic SQL Injection And Database Takeover With SQLMap 0.9
sqlmap is an open source SQL injection penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers. SQLMap consists of a very accurate detection engine, many niche features for the ultimate penetration tester and a broad range of switches lasting from database fingerprinting, over data fetching from the database, to accessing the underlying file system and executing commands on the operating system via out-of-band connections.
SQLMap v. 0.9 is out on April 10, 2011 and now consists of more features than ever with numerous improvements in coding. This time the SQL Injection engine has been re-written in v. 0.9 and the tool will be very useful for security experts, enthusiasts and hackers. The feature list of SQLMap is available over HERE.
The tool can be downloaded from the sourceforge page HERE.
Read more...
SQLMap v. 0.9 is out on April 10, 2011 and now consists of more features than ever with numerous improvements in coding. This time the SQL Injection engine has been re-written in v. 0.9 and the tool will be very useful for security experts, enthusiasts and hackers. The feature list of SQLMap is available over HERE.
The tool can be downloaded from the sourceforge page HERE.
Read more...
Automatic SQL Injection And Database Takeover With SQLMap 0.9
2011-04-24T18:38:00+05:45
Cool Samar
hacking|security|security bypass|sql injection|
Comments
Labels:
hacking,
security,
security bypass,
sql injection
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Saturday 23 April 2011
A Very Basic Guide To SSH Tunnelling To Bypass Web Filters
SSh, Secure Shell, is a program and protocol for securely logging in to and running programs on remote machines across a network, with encryption to protect the transferred information and authentication to ensure that the remote machine is the one desired; To use ssh to connect to a remote computer. In this tutorial, I'll show you how to do simple ssh tunnelling to bypass web filters.
We'll be using a ssh client in this tutorial. One such SSh client is putty and we be using putty in our tutorial. It can be downloaded from HERE. We need a working SSh account and there are lots of free as well as paid free shell providers. I'll be using one of the shell accounts for this tutorial.
After downloading putty, open the program and enter the host and port information. The screenshot below will be helpful for you.
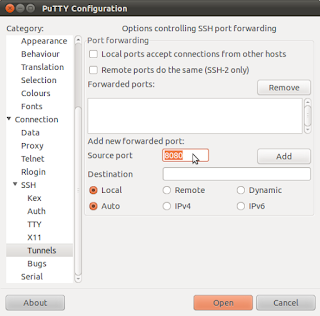
Now go to the SSh option below in the left menu of Putty. And select the tunnels submenu. Set the source port to any higher ports. I chose 8080 in my example. Then select the dynamic option. And click on Add by leaving other options as they are.
Now, click on Open and login to your SSh server. The only thing left now is to setup your favourite browser to work with the SSh tunnel. In firefox(under ubuntu), I go to Edit - Preferences - Advanced - Network - Settings to set the proper proxy configuration. The setup entry will be:
Socks host: localhost
Port: 8080
That's all for setup. Now you can use the ssh tunnel to browse webspace by bypassing web filters in your school or office. I hope it was useful. Thanks. :)
Read more...
We'll be using a ssh client in this tutorial. One such SSh client is putty and we be using putty in our tutorial. It can be downloaded from HERE. We need a working SSh account and there are lots of free as well as paid free shell providers. I'll be using one of the shell accounts for this tutorial.
After downloading putty, open the program and enter the host and port information. The screenshot below will be helpful for you.
Now go to the SSh option below in the left menu of Putty. And select the tunnels submenu. Set the source port to any higher ports. I chose 8080 in my example. Then select the dynamic option. And click on Add by leaving other options as they are.
Now, click on Open and login to your SSh server. The only thing left now is to setup your favourite browser to work with the SSh tunnel. In firefox(under ubuntu), I go to Edit - Preferences - Advanced - Network - Settings to set the proper proxy configuration. The setup entry will be:
Socks host: localhost
Port: 8080
That's all for setup. Now you can use the ssh tunnel to browse webspace by bypassing web filters in your school or office. I hope it was useful. Thanks. :)
Read more...
A Very Basic Guide To SSH Tunnelling To Bypass Web Filters
2011-04-23T17:51:00+05:45
Cool Samar
hacking|security|security bypass|tricks and tips|
Comments
Labels:
hacking,
security,
security bypass,
tricks and tips
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Subscribe to:
Posts (Atom)