Monday 21 March 2011
Graphical management of runlevel init scripts with Boot-Up Manager
I've been using boot-up manager to graphically configure and manage the init scripts run according to the run level. And its pretty useful. So I thought to share about this application in this post.
From http://www.marzocca.net/linux/bumdocs.html#introduction :
The scripts located in /etc/init.d are part of the bootup sequence of every Debian-like distro. Very often Ubuntu's documentation and guides have suggested - in order to deactivate init scripts - to change the permissions of the scripts in /etc/init.d, making them non-executable. This will have the following consequences:
* You'll get an error message at boot time (to avoid it you need to patch all the scripts);
* You are breaking the logical chain stated in debian-policy concerning runlevel configuration.
If the logic of a debian-like system boot up sequence is not very clear and familiar to you, you should not play with symlinks, permissions, etc. In order to avoid messing up your system, Boot-Up Manager will automate all of your configuration in a nice and clean graphical interface.
From http://www.marzocca.net/linux/bum.html :
Boot-Up Manager is a Perl-Gtk2 application to handle runlevels configuration of any debian derivative system. With this program the user will easily start and stop boot-up scripts, without the necessity to handle thru complex links and permissions.
Boot-Up Manager has been developed and tested on Ubuntu, but as it only relies on Perl-Gtk2 libraries, it can be run on any Debian-like system.
To install Boot-up manager under ubuntu, run the following terminal:
Deb files are available for download for other debian based systems.
In order to run the application, go to System-> Administration -> Boot-up Manager or type the following in command menu:
You could refer to the above mentioned links for more technical details on bum.
Read more...
From http://www.marzocca.net/linux/bumdocs.html#introduction :
The scripts located in /etc/init.d are part of the bootup sequence of every Debian-like distro. Very often Ubuntu's documentation and guides have suggested - in order to deactivate init scripts - to change the permissions of the scripts in /etc/init.d, making them non-executable. This will have the following consequences:
* You'll get an error message at boot time (to avoid it you need to patch all the scripts);
* You are breaking the logical chain stated in debian-policy concerning runlevel configuration.
If the logic of a debian-like system boot up sequence is not very clear and familiar to you, you should not play with symlinks, permissions, etc. In order to avoid messing up your system, Boot-Up Manager will automate all of your configuration in a nice and clean graphical interface.
From http://www.marzocca.net/linux/bum.html :
Boot-Up Manager is a Perl-Gtk2 application to handle runlevels configuration of any debian derivative system. With this program the user will easily start and stop boot-up scripts, without the necessity to handle thru complex links and permissions.
Boot-Up Manager has been developed and tested on Ubuntu, but as it only relies on Perl-Gtk2 libraries, it can be run on any Debian-like system.
To install Boot-up manager under ubuntu, run the following terminal:
sudo apt-get install bum
Deb files are available for download for other debian based systems.
In order to run the application, go to System-> Administration -> Boot-up Manager or type the following in command menu:
su-to-root -X -c bum
You could refer to the above mentioned links for more technical details on bum.
Read more...
Graphical management of runlevel init scripts with Boot-Up Manager
2011-03-21T21:40:00+05:45
Cool Samar
linux|software|ubuntu|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
LTSP deployment visit to Baglung and Myagdi
With the help of HeNN(Help Nepal Network), we've been on our visit to two schools of Baglung and Myagdi. We were the group of three, Arnab Sarkar, Bikash Kharel and me(we all are from Kathmandu University). Our deployment visit has come to an end and we are on our way back to Dhulikhel. The visit was full of fun and gave me new experience of working in team(though the team was extremely small :p). We had lots of fun in both places and received pretty good response from the local people.
Our journey started on March 4 and we took our bus to Bhimgithe-8, Khaala, Baglung. The journey was full of adventures. Thank god, the bus was third class due to which I got a chance to taste the tea without sugar (It was great, btw :D). We didn't sleep for the whole night and our dinner was at around 11 pm at night. The real adventure began when we reached Ridi, one of the more known places from Gulmi. The road was, well, so narrow that only the tires of the bus were on the road and outer parts of the bus were out of the track. A small mistake and our bus would fall down to the river and we were excited and scared at the same time. Moreover, the driver of our bus had not been sleeping for more than 24 hours so we were even more scared. On the next day of our journey, we had to face some problem with traffic police regarding the horn used in the bus.
At around 10:30 we arrived at Khaala, our first destination. We were excited to see such a big mass from such a small village for welcoming us. All the computer materials and accessories were stored in the school's storeroom and we were glad to find all the materials in the good condition after such a "ghandryaang-ghundrung" journey. The furnitures and computer room were not ready yet so we took full rest on our first day. Next day, we started to setup the LTSP clients and the task was completed in around 2 hours. We were helped by the local villagers, teachers and even the principal of the school in setting up the system. After finishing the setup, we started to train the teachers and students. Everyone seemed to be so interested with this new "computer" object and we felt so glad to see such involvement of everybody. On the next day, we again gave training to the teachers as well as students so that they would be familiar with the system. In the late hours, we provided teachers information about how to troubleshoot the general problems they might face with the system. We now had to go to Histan-6, Rima, Myagdi for our next deployment task.
Next day, we headed to Myagdi district for our next deployment at Adarsha Madhyamik Vidhyalaya, Rima, Myagdi. We spent our first night in Myagdi in Tatopani. Next day, we took a short warm shower in Tatopani and then quickly headed to Beni to catch the bus for Baisari. In next two hours, we were already in Baisari. Now one of the toughest time of our visit had come and we had to walk uphill for around 3 hours(local villagers require 1.5 hours :P). We were tired and hence decided to pass that night at Aula, 30 min below Rima. Next day, we went to Rima school and soon thought of starting our work. But unfortunately, the electricity transmission line was down and we had to wait for the next day. We faced multiple problems due to electricity and lack of materials in Rima school. Edubuntu didn't seem to like the hard disk and never wanted to install. Btw, it was not actually LTSP deployment but it was a RDP deployment. Not being successful with Edubuntu, we decided to install Windoze XP and again with more hurdles(loadshedding being the major one), we finished all the tasks. We had to stay for 4 days at Rima to finish all the tasks. Finally the system was up and we were very glad to see it working.
We are right now on our way back to Dhulikhel and we've managed a small meeting with Mahabir Pun, the MAN from Myagdi. Both deployments were successful and personally I gained lots of experience and practical knowledge(Running LTSP under virtualbox and deploying a full LTSP terminals are two entirely different things).
*Note: It was written a while ago when I was in Myagdi. I am too lazy to edit :D
Read more...
Our journey started on March 4 and we took our bus to Bhimgithe-8, Khaala, Baglung. The journey was full of adventures. Thank god, the bus was third class due to which I got a chance to taste the tea without sugar (It was great, btw :D). We didn't sleep for the whole night and our dinner was at around 11 pm at night. The real adventure began when we reached Ridi, one of the more known places from Gulmi. The road was, well, so narrow that only the tires of the bus were on the road and outer parts of the bus were out of the track. A small mistake and our bus would fall down to the river and we were excited and scared at the same time. Moreover, the driver of our bus had not been sleeping for more than 24 hours so we were even more scared. On the next day of our journey, we had to face some problem with traffic police regarding the horn used in the bus.
At around 10:30 we arrived at Khaala, our first destination. We were excited to see such a big mass from such a small village for welcoming us. All the computer materials and accessories were stored in the school's storeroom and we were glad to find all the materials in the good condition after such a "ghandryaang-ghundrung" journey. The furnitures and computer room were not ready yet so we took full rest on our first day. Next day, we started to setup the LTSP clients and the task was completed in around 2 hours. We were helped by the local villagers, teachers and even the principal of the school in setting up the system. After finishing the setup, we started to train the teachers and students. Everyone seemed to be so interested with this new "computer" object and we felt so glad to see such involvement of everybody. On the next day, we again gave training to the teachers as well as students so that they would be familiar with the system. In the late hours, we provided teachers information about how to troubleshoot the general problems they might face with the system. We now had to go to Histan-6, Rima, Myagdi for our next deployment task.
Next day, we headed to Myagdi district for our next deployment at Adarsha Madhyamik Vidhyalaya, Rima, Myagdi. We spent our first night in Myagdi in Tatopani. Next day, we took a short warm shower in Tatopani and then quickly headed to Beni to catch the bus for Baisari. In next two hours, we were already in Baisari. Now one of the toughest time of our visit had come and we had to walk uphill for around 3 hours(local villagers require 1.5 hours :P). We were tired and hence decided to pass that night at Aula, 30 min below Rima. Next day, we went to Rima school and soon thought of starting our work. But unfortunately, the electricity transmission line was down and we had to wait for the next day. We faced multiple problems due to electricity and lack of materials in Rima school. Edubuntu didn't seem to like the hard disk and never wanted to install. Btw, it was not actually LTSP deployment but it was a RDP deployment. Not being successful with Edubuntu, we decided to install Windoze XP and again with more hurdles(loadshedding being the major one), we finished all the tasks. We had to stay for 4 days at Rima to finish all the tasks. Finally the system was up and we were very glad to see it working.
We are right now on our way back to Dhulikhel and we've managed a small meeting with Mahabir Pun, the MAN from Myagdi. Both deployments were successful and personally I gained lots of experience and practical knowledge(Running LTSP under virtualbox and deploying a full LTSP terminals are two entirely different things).
*Note: It was written a while ago when I was in Myagdi. I am too lazy to edit :D
Read more...
LTSP deployment visit to Baglung and Myagdi
2011-03-21T21:09:00+05:45
Cool Samar
site news and update|
Comments
Labels:
site news and update
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday 3 March 2011
My first LTSP deployment visit
I am excited about my first LTSP(Linux Terminal Server Project) deployment visit to Baglung and Myagdi districts of Nepal. I shall not be able to write in the blog for a while because of this. I hope to have fun and make good experience in my first LTSP visit. :)
Read more...
Read more...
My first LTSP deployment visit
2011-03-03T21:38:00+05:45
Cool Samar
site news and update|
Comments
Labels:
site news and update
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Monday 28 February 2011
Autostarting programs on login in Ubuntu [How To]
If you want to start any program in your ubuntu installation whenever you login then you can just create a symbolic link in a special folder located at ~/.config/autostart/(that is somewhere inside of your home folder). The process is pretty easy and most of the guys out there might have already understood what you have to do but still I am writing the process for those who might get stuck on the way.
I'll demonstrate, as an example, how to autostart skype at the login time. As stated earlier, all you have to do is create a symbolic link to skype executable file as below. The command is typed in terminal(gnome-terminal).
Btw, to find the location of any executable in linux, you can use the which command like below:
I hope this helps. Thanks. :)
Read more...
I'll demonstrate, as an example, how to autostart skype at the login time. As stated earlier, all you have to do is create a symbolic link to skype executable file as below. The command is typed in terminal(gnome-terminal).
ln -s /usr/bin/skype ~/.config/autostart
Btw, to find the location of any executable in linux, you can use the which command like below:
which skype
I hope this helps. Thanks. :)
Read more...
Autostarting programs on login in Ubuntu [How To]
2011-02-28T21:02:00+05:45
Cool Samar
linux|tricks and tips|ubuntu|
Comments
Labels:
linux,
tricks and tips,
ubuntu
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Saturday 26 February 2011
How to get things for free in internet [Google dorks]
Well its been a few days I haven't posted. Today I have come with an interesting post that will help you get things for free in internet. Of course, it is not legal but it works in many cases but not always. And many of the results might be some craps.
Following are the list of the google dorks that will help you get some of the commercial softwares for free. Google dorks are the keyword phrases that can be searched with the google search engine.
The above dorks are just the examples. You can modify them and do some experiments on your own to search for specific domains, etc. I hope this is useful. Thanks :)
Read more...
Following are the list of the google dorks that will help you get some of the commercial softwares for free. Google dorks are the keyword phrases that can be searched with the google search engine.
intitle:"Thank You For Your Order" intext:Click Here to Download
intitle:"Thank You For Your Purchase" intext:Click Here to Download
inurl:/thankyou*.html intitle:Thank you for your order! intext:Click Here to Download
intitle:"Thank You For Your Order!" intext:download
inurl:thanks intext:"Thank You For Your Order!" "Click Here" filetype:html
intitle:"Thank You For Your Purchase" intext:Click Here to Download
inurl:/thankyou*.html intitle:Thank you for your order! intext:Click Here to Download
intitle:"Thank You For Your Order!" intext:download
inurl:thanks intext:"Thank You For Your Order!" "Click Here" filetype:html
The above dorks are just the examples. You can modify them and do some experiments on your own to search for specific domains, etc. I hope this is useful. Thanks :)
Read more...
How to get things for free in internet [Google dorks]
2011-02-26T20:15:00+05:45
Cool Samar
google hacking|hacking|internet|software|web|
Comments
Labels:
google hacking,
hacking,
internet,
software,
web
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Wednesday 23 February 2011
How to fix the USB support in virtualbox
I installed virtualbox 4 after removing the OSE version and I tried to test the USB support. But I didn't find it working so I tried few things. And on diving to the internet, I figured out that I must be the member of the group "vboxusers" to be able to have USB support in my virtualbox.
Follow the steps as stated below:
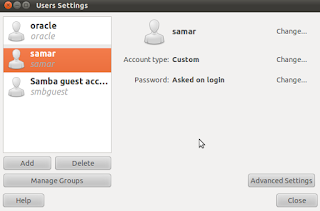
1) Go to System->Administration->Users and groups. You'll see the screen like below:
2) From there, click on Manage groups and then select the vboxusers group and edit its property. Now in the properties window, check your username as marked for the group. The screenshot below would clarify you.
Alternatively this all could be achieved by a simple command as below(Here, we are adding the user "samar" to the group vboxusers):
In order to verify that everything went well, you could type in terminal:
3) Now you will have to restart(or just logout from your account) and then re-login to your account. Now virtualbox will allow you to use USB devices. When your virtual machine is on, just go to Devices->USB devices and select the one that needs to be active.
I hope this helps you. :)
Read more...
Follow the steps as stated below:
1) Go to System->Administration->Users and groups. You'll see the screen like below:
2) From there, click on Manage groups and then select the vboxusers group and edit its property. Now in the properties window, check your username as marked for the group. The screenshot below would clarify you.
Alternatively this all could be achieved by a simple command as below(Here, we are adding the user "samar" to the group vboxusers):
samar@Techgaun:~$ sudo useradd -G vboxusers samar
In order to verify that everything went well, you could type in terminal:
samar@Techgaun:~$ grep vboxusers /etc/group
3) Now you will have to restart(or just logout from your account) and then re-login to your account. Now virtualbox will allow you to use USB devices. When your virtual machine is on, just go to Devices->USB devices and select the one that needs to be active.
I hope this helps you. :)
Read more...
How to fix the USB support in virtualbox
2011-02-23T22:19:00+05:45
Cool Samar
linux|tricks and tips|ubuntu|virtualbox|
Comments
Labels:
linux,
tricks and tips,
ubuntu,
virtualbox
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Saturday 19 February 2011
Art of hacking 2 - spyd3rm4n's guide to hacking
Earlier I posted the spyd3rm4n's guide to hacking part 1 over HERE. This is the 2nd part of the guide. Enjoy the guide.
Part II
[0x01] Common_Knowledge
[0x02] How
Sub Common_Knowledge{
It is customary that a hacker know how to hack, but it is mandatory that a hacker know how to hide his/her ass.
You DO NOT want to get caught because:
A) I'm sure you don't want to pay that hefty fine.
B) I'm positive you don't want a criminal record.
C) You probably don't want to be put on probation.
D) You put everybody you have contacted on the internet within your past at risk of being caught.
E) You WILL be frowned upon as a terrible hacker. Everyone knows, you're dumb as shit if you get caught.
F) If you find any reasons why getting caught would be a good idea, please consider the following:
Go to the local gunshop.
Purchase a powerful weapon (remember, you don't want to screw this up.)
Purchase a small magazine.
Go home, place the clip into the weapon, take off the saftey and look into the barrel of the gun and email me back
the color that flashes inside the barrel when the trigger is pulled.
}
Sub How{
What are some ways you can hide your ass? Well, good question, but there are many answers.
I have to say, that the most common way for a person to hide their e-dentity is via a proxy.
Now, one problem with the proxies, is that anyone with common sense can find out your real IP. This is the start of Forensics.
The easiest way for a person to find your IP is the find the provider of the proxy, most like CDN (CoDeeN), seeing that they are
the largest proxy releasing company on the inet. Once they contact CoDeeN (who keep records of all IP's logged into their proxy
at all times), they can find your IP and with a simple whois, can come up with the location of you or your ISP. After that, it's just
a long talk between you and your ISP to find out your information. That's if there has been illegal activity and/or you caused some
pretty hefty damage. ISP's can't release a persons information without a court order as that is an invasion of privacy. But there are
some loop holes in this system. I'm sure you have all read your ISP's fine print and Terms of Service correct? Well, it will most likely
contain something stating that hacking is illegal and that if caught, they can and will report you to the authorities etc.
Another reason is because of the easy PHP function, $_SERVER['HTTP_X_FORWARDED_FOR'] which can be used to grab your real
IP and/or block your attempt at viewing the site.
Another way of hiding your ass, which I suggest as a first part, because it is the easiest, is find a VPN. VPN stands for Virtual Private
Network. Large companies/businesses have these VPN's for their employees to operate on a local network (LAN) over WAN (Wide
Area Network). They will mask your IP with the IP that the VPN is setup on. I.E. My IP is 66.77.88.102 and the VPN IP is 24.12.21.64,
when I log into the VPN, my IP will become 24.12.21.64. This covers your IP over every protocol, it whoops Socks 4 and Socks 5 proxies
rearends. The one thing you have to worry about with a VPN, is that they too, if setup correctly, can log every IP that has used the VPN
at anytime of the day.
Now that the 2 most common ways of hiding your ip have been discussed. Let's not rule out some of the other ways. One being VNC tunneling.
This is the process of logging in to a remote administrative tool repeatedly on other servers.
Example:
Server 1 IP: 1.2.3.4
Server 2 IP: 1.2.3.5
Server 3 IP: 1.2.3.6
All servers have VNC running. I will then log into the VNC for Server 1, then I will use Server 1's VNC to log into Server 2, and repeat the process until
I am logged in on Server 3. This will hide my IP 3 times and make tracing it back even harder. But, once again, you've guessed it. It records everything.
Well, Since I'm getting pretty desperate here, why don't I go balls out?
I will hop on a VPN, then I will VNC tunnel into about 2 or 3 Servers, while logging into a VPN on each of those, then, finally, when I'm tunneled into
Server 3, I will put a VPN on, log into a Socks 4 proxy, put on a anonymous proxy, if I have to, even goto a well known web proxifying site that runs
a CGI or PHP built proxy to view the content needed. Now, picture yourself as that person who has to find your real IP. Yeah, it's gonna be a blast.
The only bad part about this is the fact that the more you log into, the slower and slower it will get. Best done on a high-speed line.
Finally, since this is a mini-book on hiding your ass, I might as well tell you that everything of anything on the internet is logged. Don't forget to clear them.
Example: SSH-
don't forget to rm -rf /var/logs*
}
- Credits : Kr3w of TheDefaced.
Part II
[0x01] Common_Knowledge
[0x02] How
Sub Common_Knowledge{
It is customary that a hacker know how to hack, but it is mandatory that a hacker know how to hide his/her ass.
You DO NOT want to get caught because:
A) I'm sure you don't want to pay that hefty fine.
B) I'm positive you don't want a criminal record.
C) You probably don't want to be put on probation.
D) You put everybody you have contacted on the internet within your past at risk of being caught.
E) You WILL be frowned upon as a terrible hacker. Everyone knows, you're dumb as shit if you get caught.
F) If you find any reasons why getting caught would be a good idea, please consider the following:
Go to the local gunshop.
Purchase a powerful weapon (remember, you don't want to screw this up.)
Purchase a small magazine.
Go home, place the clip into the weapon, take off the saftey and look into the barrel of the gun and email me back
the color that flashes inside the barrel when the trigger is pulled.
}
Sub How{
What are some ways you can hide your ass? Well, good question, but there are many answers.
I have to say, that the most common way for a person to hide their e-dentity is via a proxy.
Now, one problem with the proxies, is that anyone with common sense can find out your real IP. This is the start of Forensics.
The easiest way for a person to find your IP is the find the provider of the proxy, most like CDN (CoDeeN), seeing that they are
the largest proxy releasing company on the inet. Once they contact CoDeeN (who keep records of all IP's logged into their proxy
at all times), they can find your IP and with a simple whois, can come up with the location of you or your ISP. After that, it's just
a long talk between you and your ISP to find out your information. That's if there has been illegal activity and/or you caused some
pretty hefty damage. ISP's can't release a persons information without a court order as that is an invasion of privacy. But there are
some loop holes in this system. I'm sure you have all read your ISP's fine print and Terms of Service correct? Well, it will most likely
contain something stating that hacking is illegal and that if caught, they can and will report you to the authorities etc.
Another reason is because of the easy PHP function, $_SERVER['HTTP_X_FORWARDED_FOR'] which can be used to grab your real
IP and/or block your attempt at viewing the site.
Another way of hiding your ass, which I suggest as a first part, because it is the easiest, is find a VPN. VPN stands for Virtual Private
Network. Large companies/businesses have these VPN's for their employees to operate on a local network (LAN) over WAN (Wide
Area Network). They will mask your IP with the IP that the VPN is setup on. I.E. My IP is 66.77.88.102 and the VPN IP is 24.12.21.64,
when I log into the VPN, my IP will become 24.12.21.64. This covers your IP over every protocol, it whoops Socks 4 and Socks 5 proxies
rearends. The one thing you have to worry about with a VPN, is that they too, if setup correctly, can log every IP that has used the VPN
at anytime of the day.
Now that the 2 most common ways of hiding your ip have been discussed. Let's not rule out some of the other ways. One being VNC tunneling.
This is the process of logging in to a remote administrative tool repeatedly on other servers.
Example:
Server 1 IP: 1.2.3.4
Server 2 IP: 1.2.3.5
Server 3 IP: 1.2.3.6
All servers have VNC running. I will then log into the VNC for Server 1, then I will use Server 1's VNC to log into Server 2, and repeat the process until
I am logged in on Server 3. This will hide my IP 3 times and make tracing it back even harder. But, once again, you've guessed it. It records everything.
Well, Since I'm getting pretty desperate here, why don't I go balls out?
I will hop on a VPN, then I will VNC tunnel into about 2 or 3 Servers, while logging into a VPN on each of those, then, finally, when I'm tunneled into
Server 3, I will put a VPN on, log into a Socks 4 proxy, put on a anonymous proxy, if I have to, even goto a well known web proxifying site that runs
a CGI or PHP built proxy to view the content needed. Now, picture yourself as that person who has to find your real IP. Yeah, it's gonna be a blast.
The only bad part about this is the fact that the more you log into, the slower and slower it will get. Best done on a high-speed line.
Finally, since this is a mini-book on hiding your ass, I might as well tell you that everything of anything on the internet is logged. Don't forget to clear them.
Example: SSH-
don't forget to rm -rf /var/logs*
}
- Credits : Kr3w of TheDefaced.
Read more...
Art of hacking 2 - spyd3rm4n's guide to hacking
2011-02-19T18:25:00+05:45
Cool Samar
beginner|hacking|security|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Friday 18 February 2011
Delete empty folders with Vanity Remover
So have you ever come to the situation when you have to delete several empty folders in your hard disks? If yes, it must have been some boring shit. But now, Vanity remover is here to rescue you.
Vanity remover is a simple tool to recursively delete the empty folders off your hard disk.
More information and downloads from the Official site
Read more...
Vanity remover is a simple tool to recursively delete the empty folders off your hard disk.
More information and downloads from the Official site
Read more...
Delete empty folders with Vanity Remover
2011-02-18T23:10:00+05:45
Cool Samar
software|tricks and tips|
Comments
Labels:
software,
tricks and tips
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Subscribe to:
Posts (Atom)