Monday 25 April 2011
Keyloggers for Linux: Secretly Watch The Linux Users
For windows, there are numerous keyloggers out there with many pretty cool features but there has been none such great keylogger. But lately there have been few developments and new keyloggers have been developed for Linux platform. In this post, I'll list few keyloggers for linux I've heard about.
1. PyKeylogger - PyKeylogger is a free open source keylogger written in the python programming language, available under the terms of the GNU General Public License. It is currently available for Windows (NT/2000 and up), and Linux (using Xlib, so won't work on the console). It is primarily designed for personal backup purposes, rather than stealth keylogging. Thus, it does not make explicit attempts to hide its presence from the operating system or the user. That said, the only way it is visible is that the process name shows up in the task list, so it is not immediately apparent that there is a keylogger on the system. More on PyKeylogger
2. Logkeys - Logkeys is no more advanced than other available Linux keyloggers, but is a bit more up to date, it doesn't unreliably repeat keys and it should never crash your X. It works with serial as well as USB keyboards. More on Logkeys
3. LKL (Linux KeyLogger) - LKL is a userspace keylogger that runs under Linux on the x86 arch. LKL sniffs and logs everything that passes through the hardware keyboard port (0x60). It translates keycodes to ASCII with a keymap file. LKL Homepage
4. THC-Vlogger - THC-vlogger, an advanced linux kernel based keylogger developed by famous hacker group THC, enables the capability to log keystrokes of all administrator/user's sessions via console, serial and remote sessions (telnet, ssh), switching logging mode by using magic password, stealthily sending logged data to centralized remote server. Its smart mode can automatically detect password prompts to log only sensitive user and password information. THC-Vlogger Home
The keyloggers for Linux are not much advanced and generally lack stealth. You'll have to be creative to make those keyloggers really stealth. Anyway, I hope this list gives you a start to know about linux keyloggers.
Read more...
1. PyKeylogger - PyKeylogger is a free open source keylogger written in the python programming language, available under the terms of the GNU General Public License. It is currently available for Windows (NT/2000 and up), and Linux (using Xlib, so won't work on the console). It is primarily designed for personal backup purposes, rather than stealth keylogging. Thus, it does not make explicit attempts to hide its presence from the operating system or the user. That said, the only way it is visible is that the process name shows up in the task list, so it is not immediately apparent that there is a keylogger on the system. More on PyKeylogger
2. Logkeys - Logkeys is no more advanced than other available Linux keyloggers, but is a bit more up to date, it doesn't unreliably repeat keys and it should never crash your X. It works with serial as well as USB keyboards. More on Logkeys
3. LKL (Linux KeyLogger) - LKL is a userspace keylogger that runs under Linux on the x86 arch. LKL sniffs and logs everything that passes through the hardware keyboard port (0x60). It translates keycodes to ASCII with a keymap file. LKL Homepage
4. THC-Vlogger - THC-vlogger, an advanced linux kernel based keylogger developed by famous hacker group THC, enables the capability to log keystrokes of all administrator/user's sessions via console, serial and remote sessions (telnet, ssh), switching logging mode by using magic password, stealthily sending logged data to centralized remote server. Its smart mode can automatically detect password prompts to log only sensitive user and password information. THC-Vlogger Home
The keyloggers for Linux are not much advanced and generally lack stealth. You'll have to be creative to make those keyloggers really stealth. Anyway, I hope this list gives you a start to know about linux keyloggers.
Read more...
Keyloggers for Linux: Secretly Watch The Linux Users
2011-04-25T22:19:00+05:45
Cool Samar
hacking|keyloggers|linux|
Comments
Labels:
hacking,
keyloggers,
linux
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Installing Adobe Photoshop CS5 In Ubuntu [How To]
In this tutorial, I will guide you through how to install and fully run Adobe Photoshop CS5 without any errors. We will be installing the Adobe Photoshop CS5 Portable version available for free in internet.
After downloading the installer for Adobe Photoshop CS5 Portable, you will have to first chmod the exe file so that it can be executed.
Now, run the installer and the photoshop installation will complete without any errors. The problem with this portable photoshop cs5 installation is that it will install correctly but might produce the runtime error complaining about the incorrect loading of C runtime environment. The error you are likely to encounter is similar to something below:
To fix this error, I copied all the files from WinSxS folder from my windows XP OS to the wine's C:\windows\WinSxS\. For this, copy all the files of WinSxS folder to USB and then to your Ubuntu OS(or if you are on VM like me, copy paste via the Virtual Shared folders feature). Now, go to Applications - Wine - Browse C: Drive and then navigate to Windows - WinSxS folder. Paste all the WinSxS contents you just copied from windows OS to this folder. See the screenshots below if you are confused from where to copy and where to paste:
Now try to run photoshop portable and you will probably face the error as below:
Now, go to Applications - Wine - Configure Wine and then from the Applications tab, click on Add Application and add the photoshop portable's executable located at $HOME/.wine/dosdevices/c:/PhotoshopPortable/App/PhotoshopCS5. After adding application, select Windows XP from Windows Version dropdown list. Click on Apply and now your photoshop CS5 portable should work without any error in Ubuntu.
I hope this helps. :)
Read more...
After downloading the installer for Adobe Photoshop CS5 Portable, you will have to first chmod the exe file so that it can be executed.
chmod +x Photoshop_Portable_12.0_en-fr-de-es-it-ru-zh-tw.paf.exe
Now, run the installer and the photoshop installation will complete without any errors. The problem with this portable photoshop cs5 installation is that it will install correctly but might produce the runtime error complaining about the incorrect loading of C runtime environment. The error you are likely to encounter is similar to something below:
Microsoft Visual C++ Runtime Library
Runtime Error!
Program C:\PhotoshopPortable\PhotoshopPortable.exe
R6034
An application has made an attempt to load the C runtime library incorrectly.
Please contact the application's support team for more information
Runtime Error!
Program C:\PhotoshopPortable\PhotoshopPortable.exe
R6034
An application has made an attempt to load the C runtime library incorrectly.
Please contact the application's support team for more information
To fix this error, I copied all the files from WinSxS folder from my windows XP OS to the wine's C:\windows\WinSxS\. For this, copy all the files of WinSxS folder to USB and then to your Ubuntu OS(or if you are on VM like me, copy paste via the Virtual Shared folders feature). Now, go to Applications - Wine - Browse C: Drive and then navigate to Windows - WinSxS folder. Paste all the WinSxS contents you just copied from windows OS to this folder. See the screenshots below if you are confused from where to copy and where to paste:
Now try to run photoshop portable and you will probably face the error as below:
Could not complete your request Unable to initialize windowing system. Terminating.
Now, go to Applications - Wine - Configure Wine and then from the Applications tab, click on Add Application and add the photoshop portable's executable located at $HOME/.wine/dosdevices/c:/PhotoshopPortable/App/PhotoshopCS5. After adding application, select Windows XP from Windows Version dropdown list. Click on Apply and now your photoshop CS5 portable should work without any error in Ubuntu.
I hope this helps. :)
Read more...
Installing Adobe Photoshop CS5 In Ubuntu [How To]
2011-04-25T21:04:00+05:45
Cool Samar
tricks and tips|ubuntu|wine|
Comments
Labels:
tricks and tips,
ubuntu,
wine
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Sunday 24 April 2011
Automatic SQL Injection And Database Takeover With SQLMap 0.9
sqlmap is an open source SQL injection penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers. SQLMap consists of a very accurate detection engine, many niche features for the ultimate penetration tester and a broad range of switches lasting from database fingerprinting, over data fetching from the database, to accessing the underlying file system and executing commands on the operating system via out-of-band connections.
SQLMap v. 0.9 is out on April 10, 2011 and now consists of more features than ever with numerous improvements in coding. This time the SQL Injection engine has been re-written in v. 0.9 and the tool will be very useful for security experts, enthusiasts and hackers. The feature list of SQLMap is available over HERE.
The tool can be downloaded from the sourceforge page HERE.
Read more...
SQLMap v. 0.9 is out on April 10, 2011 and now consists of more features than ever with numerous improvements in coding. This time the SQL Injection engine has been re-written in v. 0.9 and the tool will be very useful for security experts, enthusiasts and hackers. The feature list of SQLMap is available over HERE.
The tool can be downloaded from the sourceforge page HERE.
Read more...
Automatic SQL Injection And Database Takeover With SQLMap 0.9
2011-04-24T18:38:00+05:45
Cool Samar
hacking|security|security bypass|sql injection|
Comments
Labels:
hacking,
security,
security bypass,
sql injection
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Saturday 23 April 2011
A Very Basic Guide To SSH Tunnelling To Bypass Web Filters
SSh, Secure Shell, is a program and protocol for securely logging in to and running programs on remote machines across a network, with encryption to protect the transferred information and authentication to ensure that the remote machine is the one desired; To use ssh to connect to a remote computer. In this tutorial, I'll show you how to do simple ssh tunnelling to bypass web filters.
We'll be using a ssh client in this tutorial. One such SSh client is putty and we be using putty in our tutorial. It can be downloaded from HERE. We need a working SSh account and there are lots of free as well as paid free shell providers. I'll be using one of the shell accounts for this tutorial.
After downloading putty, open the program and enter the host and port information. The screenshot below will be helpful for you.
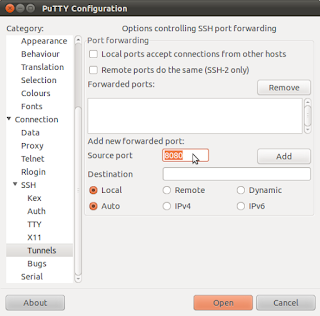
Now go to the SSh option below in the left menu of Putty. And select the tunnels submenu. Set the source port to any higher ports. I chose 8080 in my example. Then select the dynamic option. And click on Add by leaving other options as they are.
Now, click on Open and login to your SSh server. The only thing left now is to setup your favourite browser to work with the SSh tunnel. In firefox(under ubuntu), I go to Edit - Preferences - Advanced - Network - Settings to set the proper proxy configuration. The setup entry will be:
Socks host: localhost
Port: 8080
That's all for setup. Now you can use the ssh tunnel to browse webspace by bypassing web filters in your school or office. I hope it was useful. Thanks. :)
Read more...
We'll be using a ssh client in this tutorial. One such SSh client is putty and we be using putty in our tutorial. It can be downloaded from HERE. We need a working SSh account and there are lots of free as well as paid free shell providers. I'll be using one of the shell accounts for this tutorial.
After downloading putty, open the program and enter the host and port information. The screenshot below will be helpful for you.
Now go to the SSh option below in the left menu of Putty. And select the tunnels submenu. Set the source port to any higher ports. I chose 8080 in my example. Then select the dynamic option. And click on Add by leaving other options as they are.
Now, click on Open and login to your SSh server. The only thing left now is to setup your favourite browser to work with the SSh tunnel. In firefox(under ubuntu), I go to Edit - Preferences - Advanced - Network - Settings to set the proper proxy configuration. The setup entry will be:
Socks host: localhost
Port: 8080
That's all for setup. Now you can use the ssh tunnel to browse webspace by bypassing web filters in your school or office. I hope it was useful. Thanks. :)
Read more...
A Very Basic Guide To SSH Tunnelling To Bypass Web Filters
2011-04-23T17:51:00+05:45
Cool Samar
hacking|security|security bypass|tricks and tips|
Comments
Labels:
hacking,
security,
security bypass,
tricks and tips
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
How To Steal Various Keylogger's Log
Keylogger is a device or program that captures activities from an input device. Malicious people can make use of keyloggers to capture personal information being input into a computer system. Many of these keyloggers have the feature of uploading the log to some pre-defined(set by hackers) FTP servers. We can exploit this feature of keyloggers with the help of our Big Daddy, Google to obtain the logs of these keyloggers.
There are numerous keyloggers out there in the market and they provide this useful feature of FTP uploading of logs. But, the google is so powerful that it also indexes these log files. We can use the texts that are generally used by keyloggers to write in the text file. For example, following is the format of how iStealer, one of the widely used stealer, records the log through FTP.
So, we can use the terms such as Program, Url/Host, Login, etc. as the search keywords. The following search phrase would then reveal the iStealer's log.
You can creatively specify the particular hosts or programs of which you want the login information. Moreover, you might also want to use the Date feature of advanced google search to find the latest results as they will have more likelyhood to work.
Another log format of some other keylogger is something like below so you can figure out the possible dork for this format.
You can actually experiment on your own to create new useful dorks. Many times, you will find good stuffs using these dorks. Just be creative with what you look for. I hope this guides you a little. :)
Read more...
There are numerous keyloggers out there in the market and they provide this useful feature of FTP uploading of logs. But, the google is so powerful that it also indexes these log files. We can use the texts that are generally used by keyloggers to write in the text file. For example, following is the format of how iStealer, one of the widely used stealer, records the log through FTP.
Program: Firefox
Url/Host: http://www.google.com
Login: xxxxx
Password: xxxxx
Computer: samar-pc
Date: 2011-04-23 01:33:03
Ip: 116.90.*.*
Url/Host: http://www.google.com
Login: xxxxx
Password: xxxxx
Computer: samar-pc
Date: 2011-04-23 01:33:03
Ip: 116.90.*.*
So, we can use the terms such as Program, Url/Host, Login, etc. as the search keywords. The following search phrase would then reveal the iStealer's log.
Program: Url/Host: Login: Password: Computer: Date: Ip:
You can creatively specify the particular hosts or programs of which you want the login information. Moreover, you might also want to use the Date feature of advanced google search to find the latest results as they will have more likelyhood to work.
Another log format of some other keylogger is something like below so you can figure out the possible dork for this format.
APPLICATION : Firefox 4.0
URL : https://www.facebook.com
USERNAME : samar
PASSWORD : 144334@&%
URL : https://www.facebook.com
USERNAME : samar
PASSWORD : 144334@&%
You can actually experiment on your own to create new useful dorks. Many times, you will find good stuffs using these dorks. Just be creative with what you look for. I hope this guides you a little. :)
Read more...
How To Steal Various Keylogger's Log
2011-04-23T16:42:00+05:45
Cool Samar
google hacking|hacking|tricks and tips|
Comments
Labels:
google hacking,
hacking,
tricks and tips
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Thursday 21 April 2011
Practise, Learn and Master Web Application Hacking With DVWA
DVWA, which stands for Damn Vulnerable Web Application, is a PHP/MySQL web application that is damn vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, help web developers better understand the processes of securing web applications and aid teachers/students to teach/learn web application security in a class room environment.
The DVWA v. 1.07 can be downloaded from HERE.
You will need to install Apache+PHP+MySQL environment(use LAMPP or XAMPP packages) to run and test this web application. This will definitely help you learn to spot web vulnerabilities of the varied levels. I hope this was useful. :)
Read more...
The DVWA v. 1.07 can be downloaded from HERE.
You will need to install Apache+PHP+MySQL environment(use LAMPP or XAMPP packages) to run and test this web application. This will definitely help you learn to spot web vulnerabilities of the varied levels. I hope this was useful. :)
Read more...
Practise, Learn and Master Web Application Hacking With DVWA
2011-04-21T23:04:00+05:45
Cool Samar
beginner|cross site scripting|file inclusion|hacking|remote code exection|security|security bypass|sql injection|
Comments
Labels:
beginner,
cross site scripting,
file inclusion,
hacking,
remote code exection,
security,
security bypass,
sql injection
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Tuesday 19 April 2011
Enable Network Play Without Lag/Freezes In Counter Strike [How To]
Recently I had posted about how to have counter strike 1.6 run under linux but today when I was just testing to see how well the network play works, I found that the game freezes after connecting to the CT server. I searched on google and found a perfect solution for it.
I've tested this on the installation of Counter Strike : Condition Zero but should also work in Counter Strike 1.6.
The motd.txt file in the cstrike and czero can not be rendered properly by WINE so the game freezes. To solve this problem, we remove the motd.txt file and then, we create a new read only file with the name motd_temp.html which should be empty and there should be no problem rendering this new file as its just an empty file.
If there already exists the motd_temp.html in those directories, be sure to delete them and create a new empty file. To change the permission to read only, you can use the chmod command as below:
Now, you can play the counter strike in lan or with any server without any lag or freezes. Happy gaming. :)
Read more...
I've tested this on the installation of Counter Strike : Condition Zero but should also work in Counter Strike 1.6.
The motd.txt file in the cstrike and czero can not be rendered properly by WINE so the game freezes. To solve this problem, we remove the motd.txt file and then, we create a new read only file with the name motd_temp.html which should be empty and there should be no problem rendering this new file as its just an empty file.
If there already exists the motd_temp.html in those directories, be sure to delete them and create a new empty file. To change the permission to read only, you can use the chmod command as below:
chmod +r-wx motd_temp.html
Now, you can play the counter strike in lan or with any server without any lag or freezes. Happy gaming. :)
Read more...
Enable Network Play Without Lag/Freezes In Counter Strike [How To]
2011-04-19T23:05:00+05:45
Cool Samar
game|linux|ubuntu|
Comments
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Sunday 17 April 2011
How To Steal Stored Passwords From Firefox
Many of us use the Firefox's built-in password manager to remember and store the password of the sites we login to frequently. While this can be very useful feature, it can be exploited by anyone with physical(or any other form of access to the filesystem) access to know the saved passwords of the user. In this post, I will discuss how you can view and save the stored passwords of your friends for future reference.
When we select "Remember Me" option to store passwords, the passwords are stored in two files.
1.key3.db
2. signons.sqlite
These two files are in the profile directory of the mozilla firefox application data for the respective user. Profile folders are placed in a common location by default but are named randomly for additional security (e.g., "xxxxxxxx.default" is the profile folder name for the "default" profile, where xxxxxxxx represents a random strung of characters). This directory is available at different places according to the distribution.
Under windows: %APPDATA%\Mozilla\Firefox\Profiles folder will list the profiles and you can open any of the profiles from there.
Under linux: ~/.mozilla/firefox/xxxxxxxx.default folder is the profile folder. So you can navigate to ~/.mozilla/firefox/ to view the profiles.
Under MAC: ~/Library/Mozilla/Firefox/Profiles/ or ~/Library/Application Support/Firefox/Profiles/ are the folders containing the profile directories.
You can follow any of the following two methods to view the stored passwords:
Method 1: In the target computer, go to Edit->Preferences->Security and click on Saved Passwords and then click on Show Passwords to view the login details of the victim in linux. In windows, you will have to go to Tools->Options->Security.
Method 2: The first method would be applicable only for viewing the login details in victim PC. Whenever you want to save these details for further reference, you will have to copy the previously mentioned two files and save to your USB drive(or maybe in mailbox). Now, all you have to do is copy these two files to the profile directory of your PC and then go to the menus mentioned in method #1.
I hope this was useful. Thanks. :)
Read more...
When we select "Remember Me" option to store passwords, the passwords are stored in two files.
1.key3.db
2. signons.sqlite
These two files are in the profile directory of the mozilla firefox application data for the respective user. Profile folders are placed in a common location by default but are named randomly for additional security (e.g., "xxxxxxxx.default" is the profile folder name for the "default" profile, where xxxxxxxx represents a random strung of characters). This directory is available at different places according to the distribution.
Under windows: %APPDATA%\Mozilla\Firefox\Profiles folder will list the profiles and you can open any of the profiles from there.
Under linux: ~/.mozilla/firefox/xxxxxxxx.default folder is the profile folder. So you can navigate to ~/.mozilla/firefox/ to view the profiles.
Under MAC: ~/Library/Mozilla/Firefox/Profiles/ or ~/Library/Application Support/Firefox/Profiles/ are the folders containing the profile directories.
You can follow any of the following two methods to view the stored passwords:
Method 1: In the target computer, go to Edit->Preferences->Security and click on Saved Passwords and then click on Show Passwords to view the login details of the victim in linux. In windows, you will have to go to Tools->Options->Security.
Method 2: The first method would be applicable only for viewing the login details in victim PC. Whenever you want to save these details for further reference, you will have to copy the previously mentioned two files and save to your USB drive(or maybe in mailbox). Now, all you have to do is copy these two files to the profile directory of your PC and then go to the menus mentioned in method #1.
I hope this was useful. Thanks. :)
Read more...
How To Steal Stored Passwords From Firefox
2011-04-17T01:19:00+05:45
Cool Samar
browser|hacking|mozilla firefox|security bypass|tricks and tips|
Comments
Labels:
browser,
hacking,
mozilla firefox,
security bypass,
tricks and tips
Bookmark this post:blogger tutorials
Social Bookmarking Blogger Widget |
Subscribe to:
Posts (Atom)